- VMware
- 24 April 2020 at 08:53 UTC
-

- 1/2
With VMware Workstation, you can create virtual machines on Windows 10 that are secured with various options implemented in VMware Workstation.
Among the options used, you will find :
- the complete encryption of the virtual machine to protect access to it, but also its configuration and the data contained therein.
- the use of secure boot of Windows 10 through the UEFI firmware and secure boot support of VMware Workstation
- securing the operations performed by the virtual machine processor with the Trusted Platform Module (TPM) version 2.0
1. Creating the virtual machine
Note that some of the options used in this tutorial may not be available on some older versions of VMware Workstation.
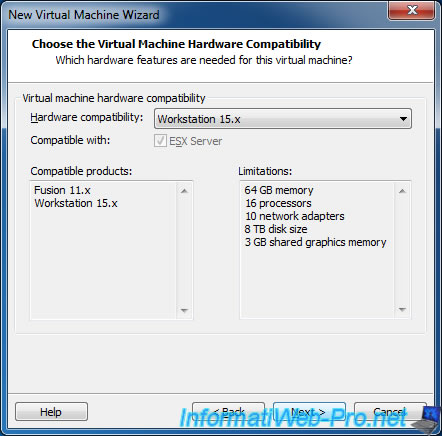
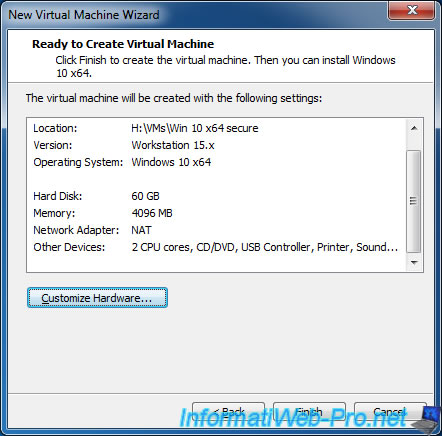
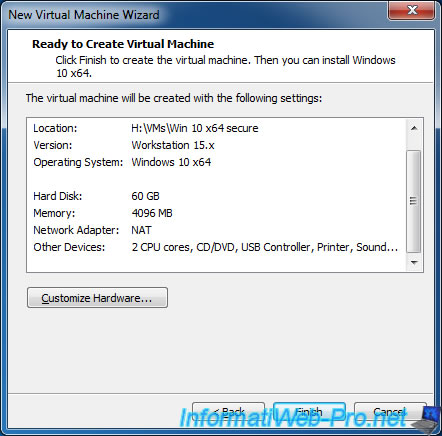
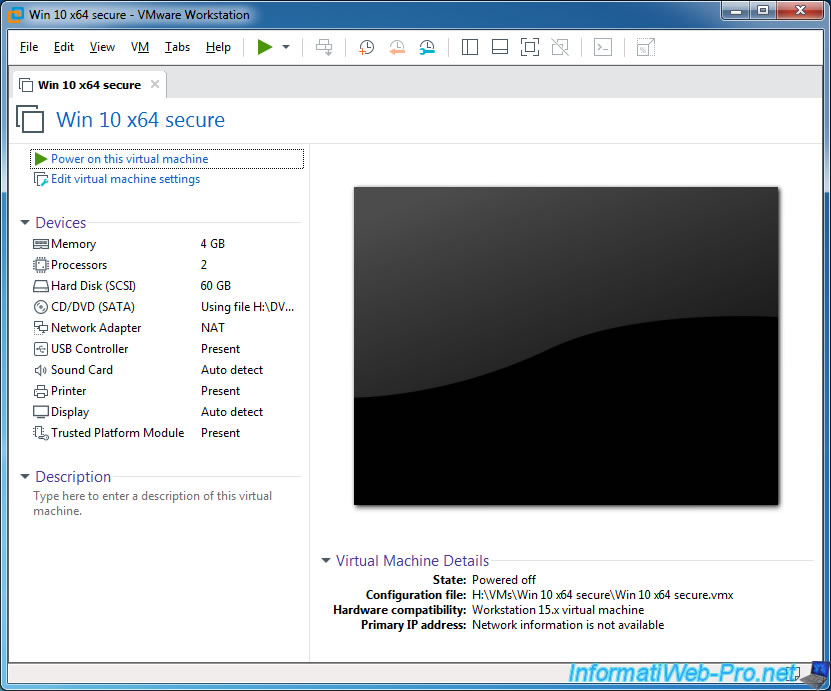
In our case, we will use VMware Workstation Pro 15.0.2 and hardware compatibility : Workstation 15.x.
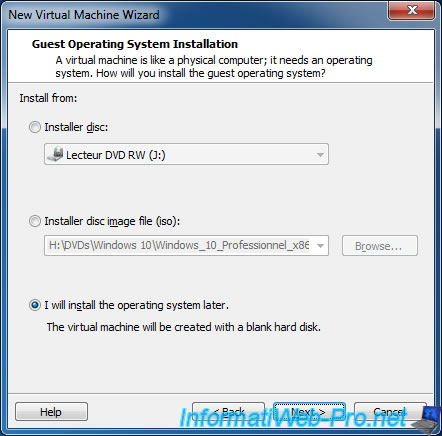
Select "I will install the operating system later".
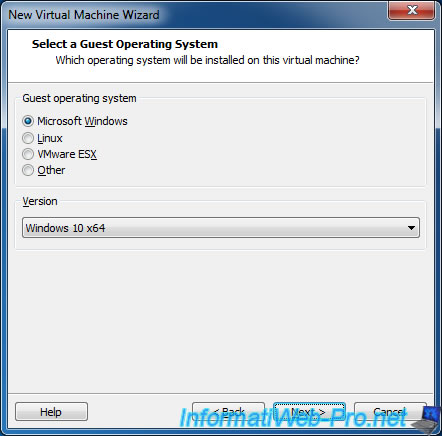
For this secure virtual machine, we will install Windows 10 as 64-bit guest OS.
Indeed, Windows 10 allows you to enjoy a secure boot (thanks to the UEFI firmware).
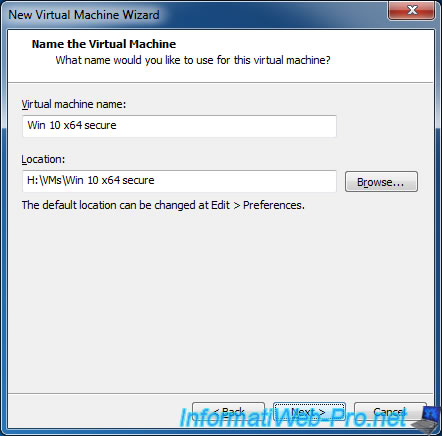
Provide a name and location for this virtual machine.
To be able to use secure boot with Windows 10, you will need to use the UEFI firmware and check the "Secure Boot" box.
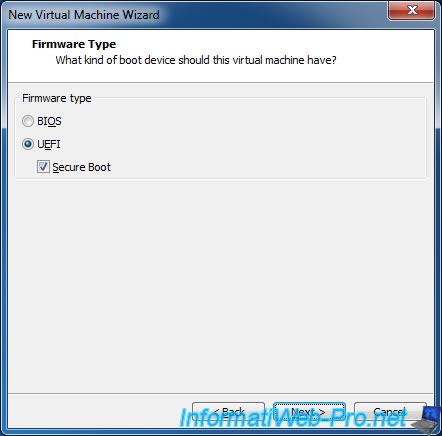
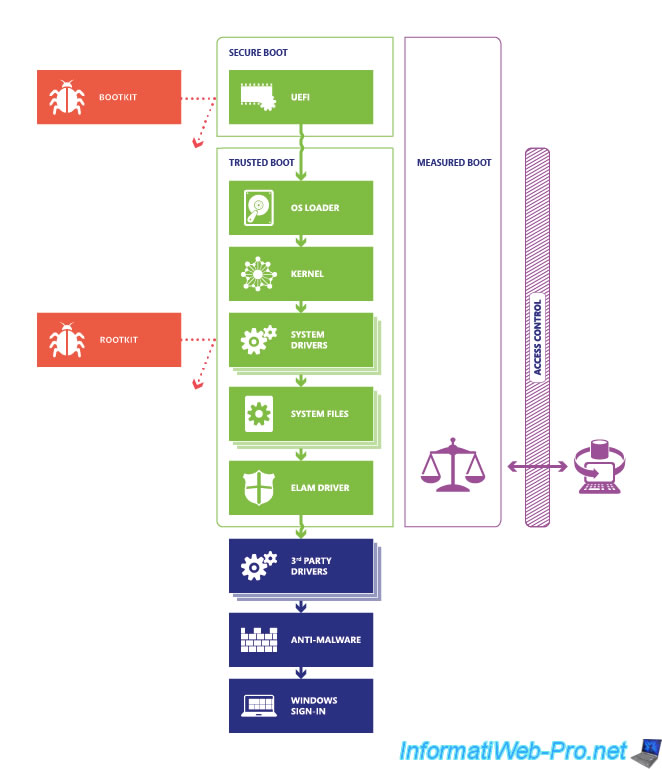
Note that the "Secure Boot" option is only available when you are using UEFI firmware and this allows you to protect against bootkits and rootkits.
For more information about how to start Windows 10 securely, visit the "Secure the Windows 10 boot process" page of the Microsoft site.
Also note that using UEFI Secure Boot requires that every boot part be signed (including : the bootloader, the operating system kernel, and the drivers installed on the OS).
Source : Enable or Disable UEFI Secure Boot for a Virtual Machine
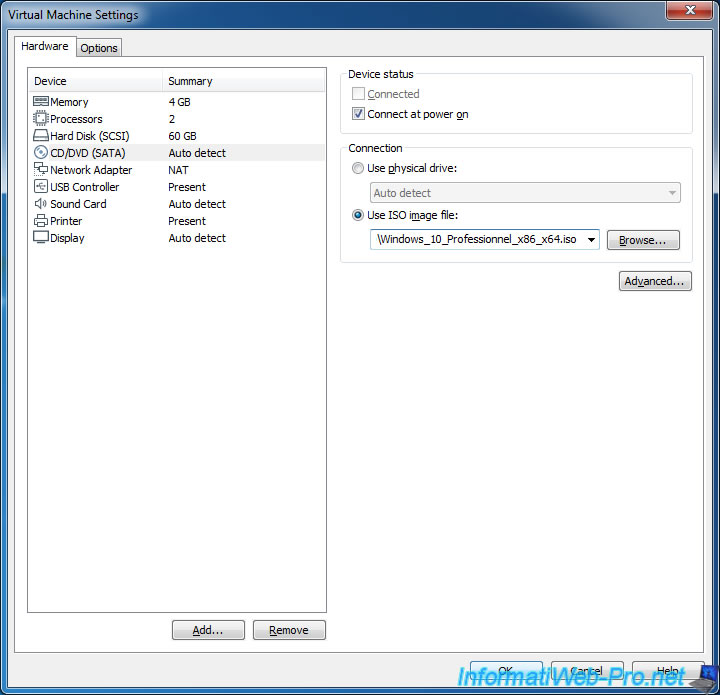
At the end of the wizard, click : Customize Hardware.
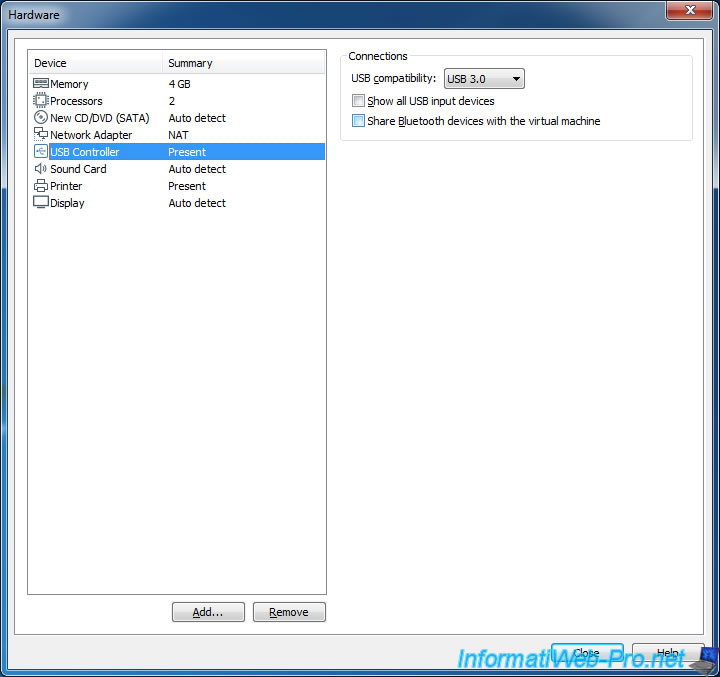
For security, you can disable the sharing of Bluetooth devices by unchecking the "Share Bluetooth devices with the virtual machine" box in the "USB Controller" section.
In the "CD/DVD (SATA)" section, select the iso file of Windows 10 (no matter the edition).
Click Finish.
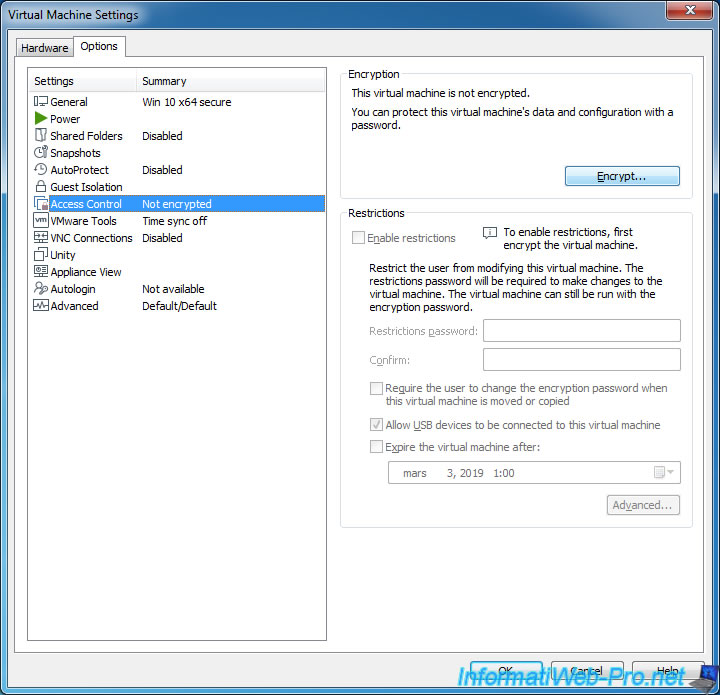
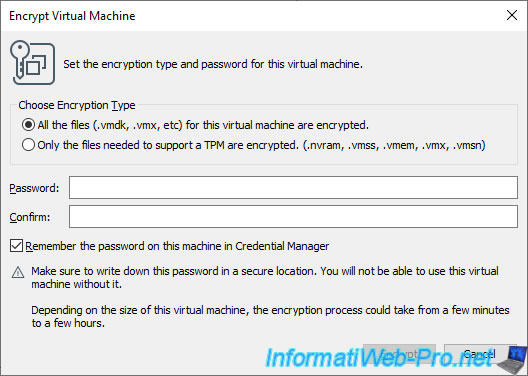
To protect your virtual machine from unauthorized access (on the host PC), you can encrypt it using the "Options -> Access Control -> Encryption" option in your virtual machine's settings.
Specify a password to entirely encrypt your virtual machine.
Note that the entire virtual machine (including configuration and virtual hard disk) will be encrypted using the password used. This means that it can't be used without the password specified here, and VMware doesn't offer an option to recover it.
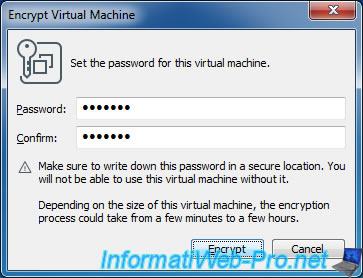
Since version 17 of VMware Workstation Pro, you will have to select the "All the files (.vmdk, .vmx, etc) for this virtual machine are encrypted" option so that the virtual machine is fully encrypted (including its virtual hard disk), as was already the case with previous versions of VMware Workstation Pro.
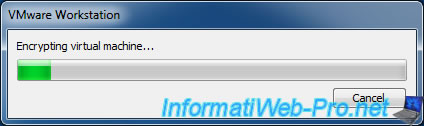
Wait while encrypting the virtual machine and its virtual hard disk.
Note that this can take a long time depending on the amount of data stored on its virtual hard disk.
Once the virtual machine is encrypted, the "The virtual machine is encrypted" message will appear.
Since version 17 of VMware Workstation, the message displayed will be "This virtual machine is fully encrypted".
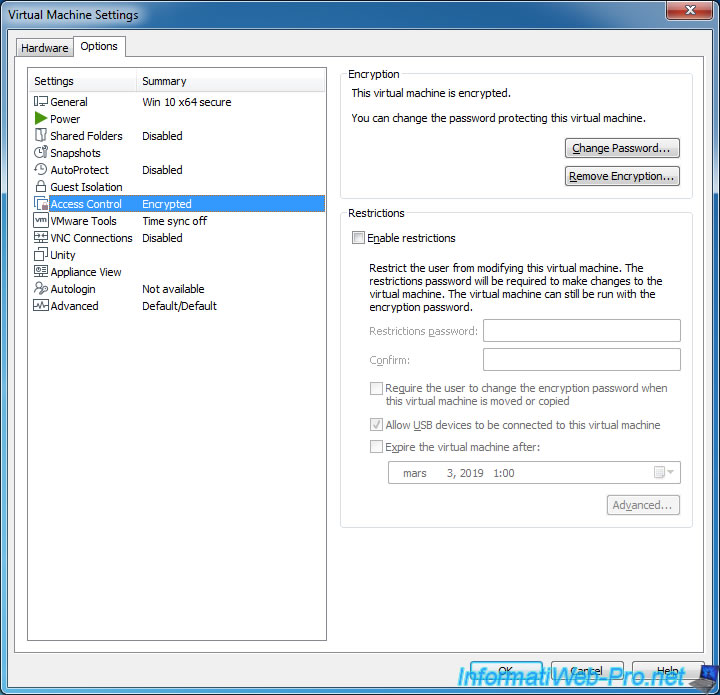
When a virtual machine is encrypted, you must specify the password in order to change its settings, start it, ...
However, when you stop an encrypted virtual machine, it will remain unlocked in VMware Workstation until VMware Workstation or the corresponding tab is closed.
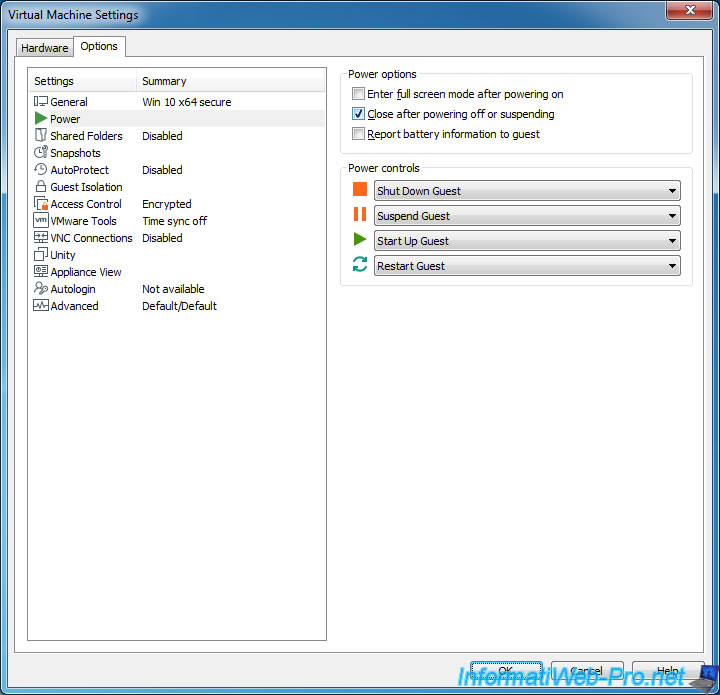
To prevent this from happening, you can enable the "Close after powering off or suspending" option in the "Power" section.
Thus, once the machine is shutdown, the virtual machine will be automatically locked and the password will be required again to use or edit it.
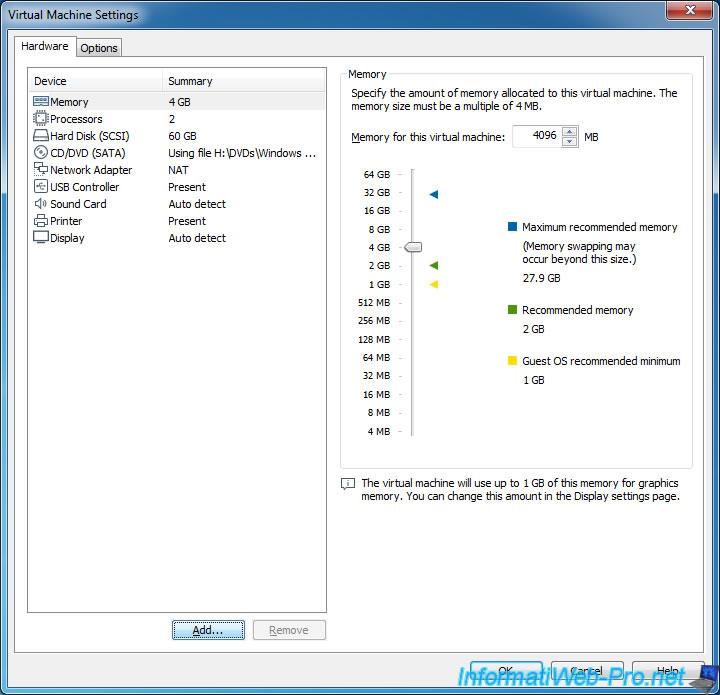
Since we will install the 64-bit version of Windows 10, we will allocate 4GB of RAM to it.
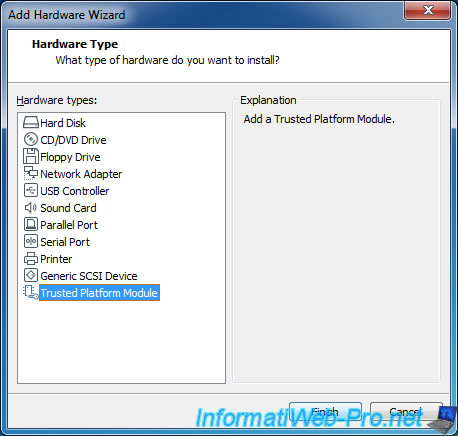
Recent Intel processors have a technology to secure a system with encryption keys.
From version 14 of VMware Workstation, it is also possible to virtualize this new technology called : Trusted Platform Module (TPM).
To use it, in the Hardware tab of the virtual machine settings, click Add and add the "Trusted Platform Module" device.
Note that once this component is added, it's strongly discouraged to remove it, as specified by VMware Workstation : Removing TPM will render all encrypted data on this VM unrecoverable.
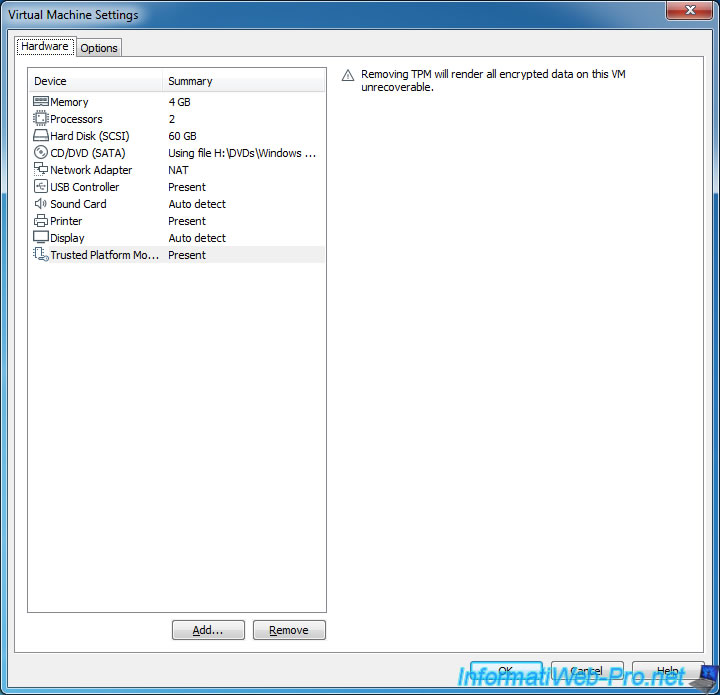
As you can see, Trusted Platform Module appears in the device list of this virtual machine.
Share this tutorial
To see also
-
VMware 3/16/2013
VMware Workstation - Boot a VM on the BIOS / EFI firmware
-
VMware 2/7/2020
VMware Workstation 15 - Installation on Linux
-

VMware 12/24/2021
VMware Workstation 15 - Slice the virtual hard disk of a VM
-

VMware 12/10/2021
VMware Workstation 15.5 - Convert a Virtual PC virtual machine to a VMware VM


You must be logged in to post a comment