Presentation of the "Active Directory Users and Computers" console on Windows Server 2016
- Windows Server
- 20 August 2021 at 13:46 UTC
-

- 3/3
3. Advanced features
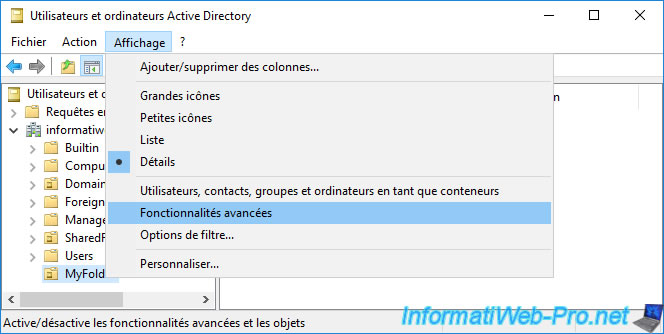
By default, not all folders and objects are displayed.
To view everything, you have to go to the "View" menu and click on "Advanced Features".
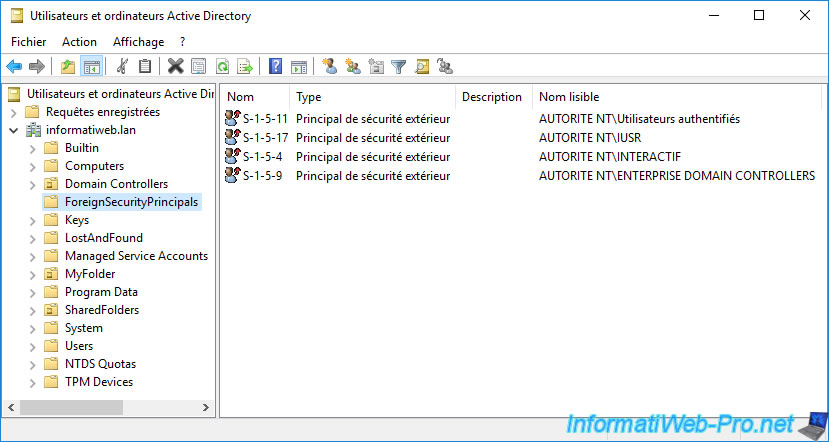
For example, by default, the "ForeignSecurityPrincipals" folder appears empty.
But once the advanced features are enabled, special accounts of the "Foreign Security Principal" type will appear.
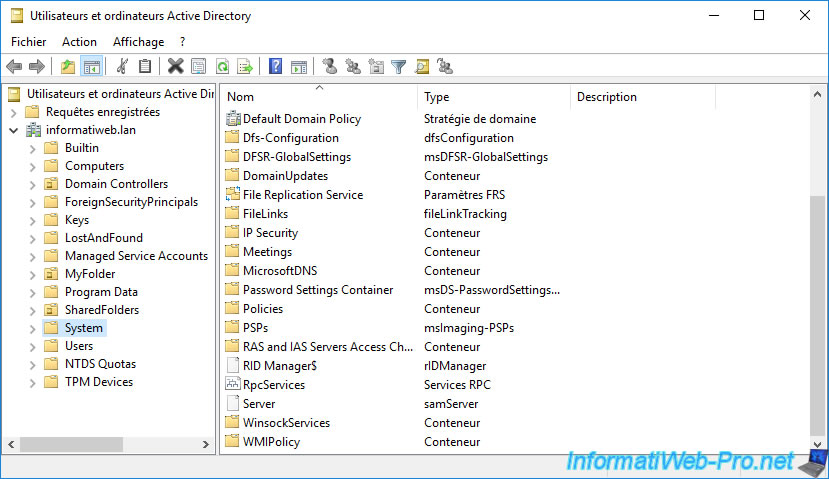
You will also find other folders, such as :
- Keys
- LostAndFound
- Program Data
- System
- NTDS Quotas
- TPM Devices
In the "System" folder of the Active Directory, you will find, for example, data about :
- the Default Domain Policy
- informations about DFS
- group policies (GPOs) : Policies
- WMI filters that you can use to filter the application of group policies : WMIPolicy
- and more
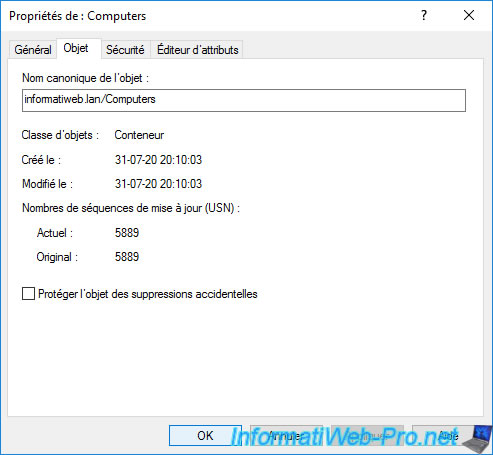
Enabling the advanced features of this "Active Directory Users and Computers" console will also add 3 tabs in the properties of each Active Directory object :
- Object
- Security
- Attribute Editor
In the "Object" tab, you will find :
- the canonical name of the object in Active Directory
- the object class used to create this object. In our case, it's a container (or "CN" in LDAP)
- date of creation and modification
- its version number called "Update Sequence Number (USN)". This number is used to resolve conflicts when replicating changes on an object from one domain controller to another.
- a "Protect object from accidental deletion" box which allows you to enable or disable the protection against the accidental deletion of an object in the Active Directory.
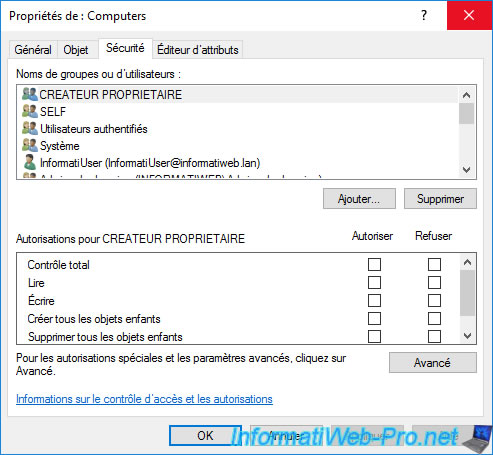
In the "Security" tab, you will find the list of permissions granted to specific users and/or user groups on the desired Active Directory object.
When you create delegations of control over some objects or a part of your Active Directory infrastructure, it's via this tab that you can modify or delete the permissions created transparently by the "Delegation of Control Wizard".
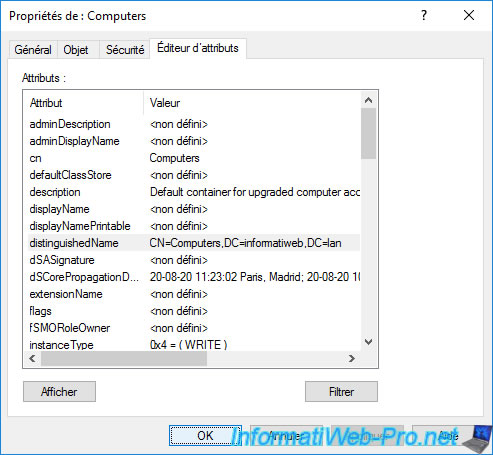
In the "Attributes Editor" tab, you can find out and modify the attributes of the desired object if you wish.
You can, for example, know the full LDAP name of an object by selecting its "distinguishedName" attribute and clicking "View" to see the full value.
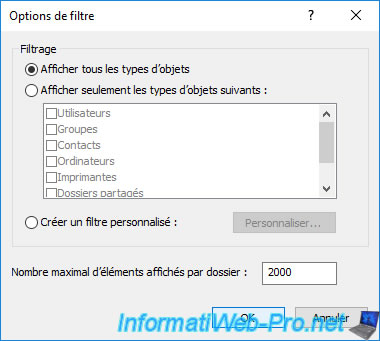
4. Filter options
If your Active Directory domain has many objects per folder, be aware that you can easily filter the type of object displayed by clicking on : View -> Filter Options.
5. Actions
To finish with this console, here are the different actions that you can perform by right-clicking on the name of your Active Directory domain.
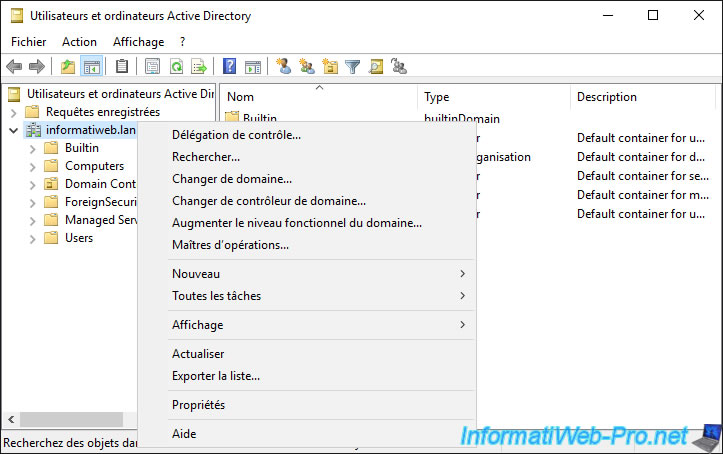
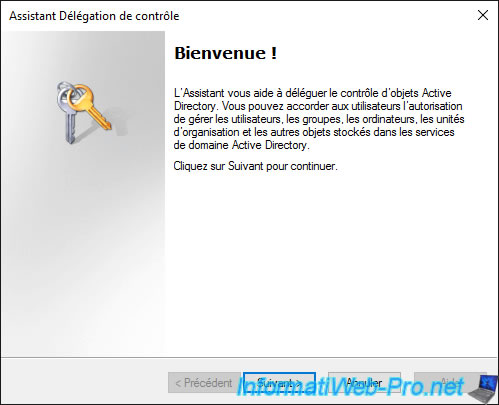
5.1. Delegate Control
To get started, you can create a delegation of control.
Delegations of control allow you to delegate the management of some tasks to some users and/or groups.
Thanks to these, you will be able to authorize users and/or user groups to :
- create, edit or delete user accounts
- change group members
- join a computer to your domain
- and more
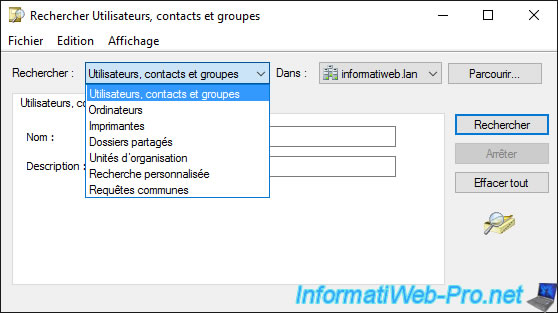
5.2. Find
You will be able to search for different types of objects in your Active Directory domain :
- Users, contacts and groups
- Computers
- Printers
- Shared folders
- Organizational units
- and more
5.3. Change Domain
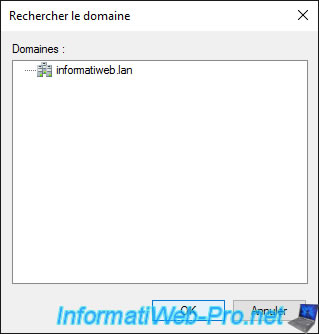
By clicking on "Change Domain", you can connect the console to another Active Directory domain (or subdomain).
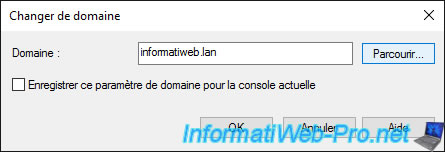
By clicking on the "Browse" button, the list of domains to which you have access will be displayed.
5.4. Change Domain Controller
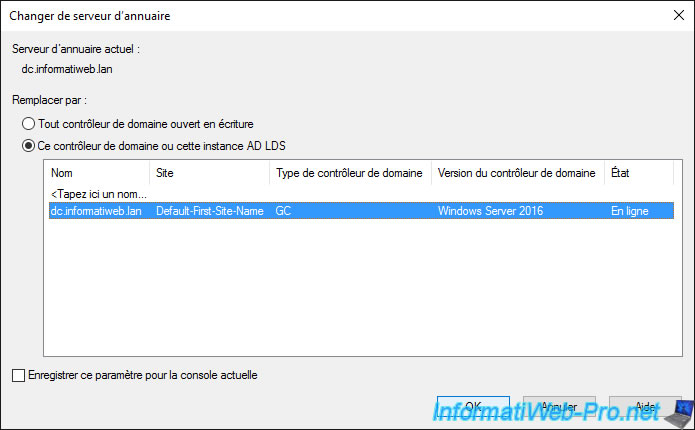
By clicking on "Change Domain Controller", you will be able to connect to another domain controller.
This can be useful in the event that you are physically on a read-only domain controller (RODC), but need to create or modify some objects.
5.5. Raise domain functional level
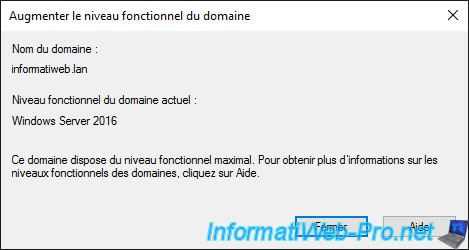
You will be able to raise the domain functional level to benefit from more features.
That being said, domain controllers running a version earlier than the one selected will therefore no longer be supported in your Active Directory infrastructure.
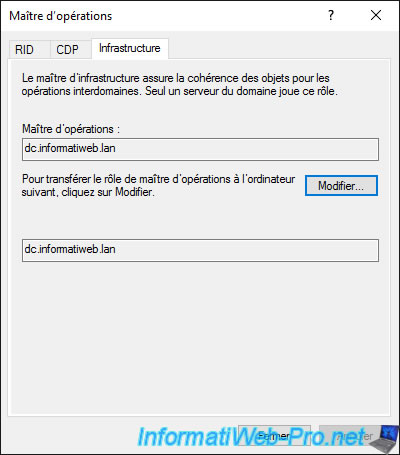
5.6. Operations Master
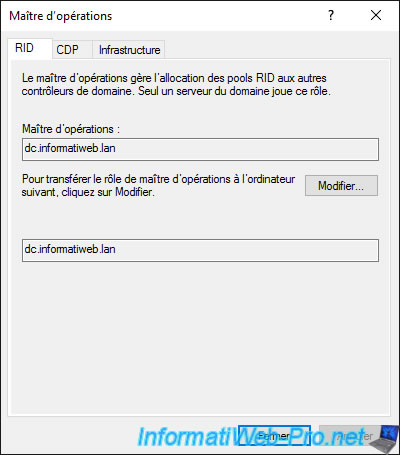
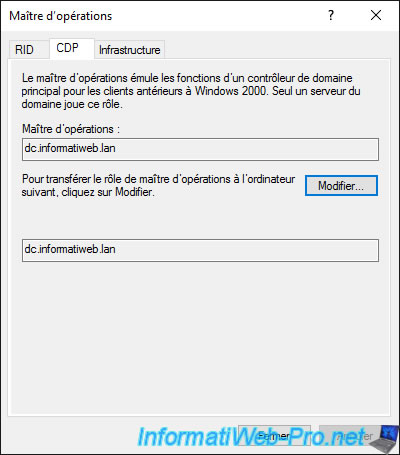
By clicking on "Operations Master", you can find out which domain controller owns which FSMO role and change the owner of these different roles if you have the rights to do so and the console is currently connected to the destination server of this role.
Note that a read-only domain controller (RODC) obviously can't be designated as master for FSMO roles since this domain controller is read-only.
Here you can know the owner for the following FSMO roles :
- RID : RID master
- CDP : PDC emulator (which means : Primary Domain Controller Emulator)
- Infrastructure : Infrastructure master
5.7. Properties
If you click on "Properties", you will find the DNS and NETBIOS domain name of your Active Directory domain, as well as the functional level of your domain and that of the forest in which it's located.

5.8. Resultant Set of Policy (Planning)
If you click on "All Tasks -> Resultant Set of Policy (Planning)", you can quickly test the application of your group policies.
Knowing that this is not 100% reliable, as there is often a difference between what you configure in policies and what is applied and/or supported by client PCs.
It's therefore important to not rely solely on the result that this feature will show you.
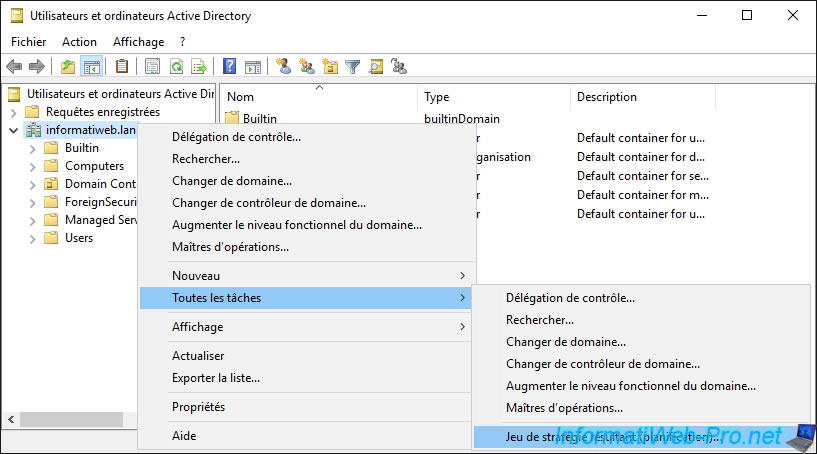
You select a computer and a user to test both the "Computer Configuration" and the "User Configuration" of your Group Policies (GPO).
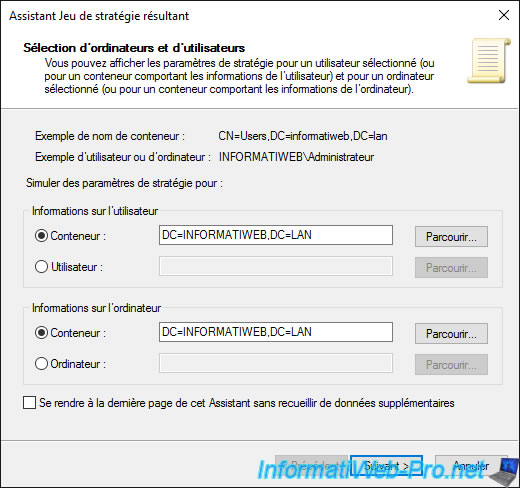
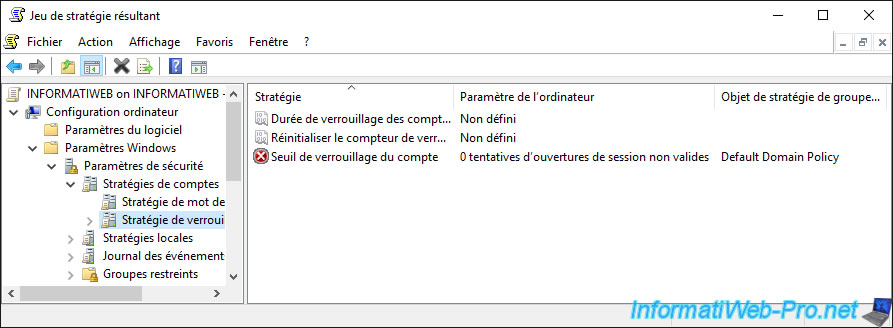
And this "Resultant Set of Policy" feature shows you what the client PC will receive as a configuration.
And it tells you which settings are set or not, what value has been set for them, and from which GPO those settings come from.
Share this tutorial
To see also
-

Windows Server 4/16/2021
Windows Server - AD DS - How Active Directory replication works
-
Windows Server 4/30/2021
Windows Server - AD DS - Overview of Active Directory functional levels
-
Windows Server 4/3/2021
Windows Server - AD DS - The basics of Active Directory
-
Windows Server 5/21/2021
WS 2016 - AD DS - Add a domain controller to an existing AD domain

No comment