- Articles
- 08 September 2023 at 07:39 UTC
-

When working in a company, it's important to be able to secure connections to ensure confidentiality and integrity, as well as to ensure that you are communicating with the right person or the right server.
For this, you will need to use encryption, as well as digital signatures (certificates).
Here is a short introduction to these notions of encryption and digital signatures (certificates).
- Why use encryption ?
- Uses of encryption
- Symmetric or asymmetric encryption ?
- Digital signatures
- Hash values
- Generating random numbers for encryption
1. Why use encryption ?
When 2 peripherals (servers, computers, smartphones, ...) communicate via the network (including via the Internet), the data they transmit to each other is sent in the clear.
Which means anyone can see this data quite easily if they are on the same network or between devices (Man in the Middle (MITM)).
Worse, it means someone with bad intentions could potentially alter what was sent.
This person could therefore modify the message that someone sent you to modify the account number to which you must pay the money for a product that you have purchased, for example. Without you being able to know that the original message has been modified.
To avoid this problem, you must encrypt the data to be sent over the network.
- Encrypt = make data unreadable by anyone except the recipient
- Decrypt = restore original data from received encrypted data
To send data securely over the network, the sender must encrypt the data using an encryption algorithm (such as : DES, AES, ...) and an encryption key (symmetric or asymmetric), then send this encrypted data to the recipient.
Then, this recipient will have to use the same encryption algorithm, as well as the appropriate encryption key to be able to decrypt the data you sent to them.
This means that if an ill-intentioned person (thus not having the appropriate key) intercepts the data which has passed through the network, it will not be able to decrypt them (or very difficult).
2. Uses of encryption
Using encryption has several uses :
- data confidentiality : prevents anyone from reading the data, except its recipient
- data integrity : prevents modification of data
- authentication : ensures that the data has been sent by the right person
- non-repudiation : the sender of the data sent can't deny that he sent this data
Thus, thanks to encryption, you can be sure :
- of the identity of the sender of a message, as well as the message received couldn't be modified on the way
- that you connect to the right server (whether it's a website, a file server (FTP), ...) and not to a hacker server that tries to pretend to be the original server
- and more
Currently, encryption is used in many cases :
- secure access to a website (that of your bank, that of your company, that allowing access to your e-mails, ...).
- secure access to a file server (so that the credentials used can't be recovered or so that the transferred files can't be recovered by a hacker, for example)
- secure access to a message server (whether it's an IMAP or POP server allowing you to download your e-mails or the SMTP server which allows you to send them)
- create a secure tunnel between 2 devices (a computer, a server, a smartphone, ... and a VPN server)
- create a secure tunnel (VPN tunnel via IPsec or other) between 2 physical sites (physical locations) to access the data of your headquarters in Brussels from the Paris office for example
- protect the data on your computer against unauthorized access using technologies such as BitLocker or TrueCrypt, for example
- and more
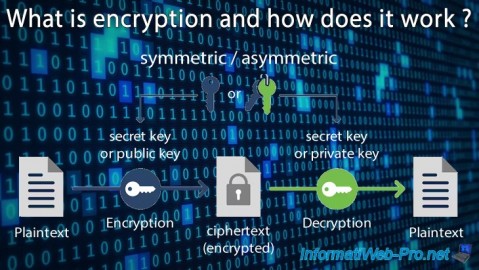
3. Symmetric or asymmetric encryption ?
As explained previously, to encrypt data, you must use an encryption algorithm and a key.
However, to encrypt and decrypt data, it's possible to use symmetric or asymmetric encryption.
When using symmetric encryption, the key used to encrypt the data is the same key used to decrypt the data.
But, if you use asymmetric encryption, the key used to encrypt the data (private key) will be different from the one used to decrypt the data (public key).
Info : when you create your own certification authority, you are creating what is called a PKI.
Meaning : Public Key Infrastructure. It's therefore asymmetric encryption that will be mainly used by it.
3.1. Symmetric Encryption (Secret Key Encryption)
When using a symmetric encryption algorithm, you will need to use a unique key that will be used to encrypt and decrypt the data.
In this case, the data will be encrypted in blocks.
Among the known symmetric encryption algorithms, you will find :
- Data Encryption Standard (DES)
- TripleDES (3DES)
- Advanced Encryption Standard (AES)
Important : this key must therefore :
- remain secret : DO NOT communicate it to a third party
- be stored in a secure place : a place where no one can see it or a location that no one can access except you
Advantages :
- fast encryption algorithm, because it uses only one key, the size of which is a maximum of 256 bits (64 bits for DES and 3DES, 128 bits, 192 bits or 256 bits for AES)
- handy for encrypting large amounts of data
Disadvantages :
- the 2 parties (users, for example) must have already agreed on the algorithm and the key to be used
- you must use an already secure means to communicate the key to the other party (user, computer, ...).
Which can be easily solved by using asymmetric encryption. Thus, the key is sent securely.
Quick example :
- the sender encrypts a message using an algorithm and key known to the recipient
- the sender sends the encrypted message to the recipient
- the recipient receives the encrypted message
- the recipient decrypts the received message using the same algorithm and the same key (information on which the 2 parties had previously agreed)
In the example above, if a third party succeeds in recovering the data which has passed through the network, this person will not be able to decrypt the recovered data.
Indeed, it knows neither the algorithm nor the key used to decrypt the recovered data.
3.2. Asymmetric Encryption (Public Key Encryption)
When using an asymmetric encryption algorithm (or public key encryption), you will need a pair of keys (a private key and a public key).
If we talk about asymmetric encryption, it's simply because the data is encrypted with one key and these can only be decrypted with the other key.
Important : as its name suggests, the private key must remain private (secret), unlike the public key which can be communicated to anyone.
Note that the private key and the public key are mathematically related.
Data that you encrypt with the public key can only be decrypted with the private key.
In the other direction, data encrypted with the private key can only be verified with the public key.
Among the known asymmetric encryption algorithms, you will find :
- RSA
- DSA (Digital Signature Algorithm)
- Diffie-Hellman
Advantages :
- the key used to encrypt the data is different from that used to decrypt the same data
- the key size is larger, which makes it possible to better secure the data.
Disadvantages :
- slower, because it uses larger keys
- the amount of data that asymmetric encryption algorithms can encrypt is mathematically limited (which is particularly the case with RSA).
For this reason, asymmetric encryption is generally used to encrypt only the key and the initialization vector.
Then the data is encrypted using the desired symmetric cipher.
Quick example : Tom wants to send a message to Lionel :
- to start, Lionel generates a pair of keys (public key / private key)
- Tom asks for Lionel's public key to be able to send him a message
- Lionel sends his public key to Tom
- Tom uses this public key to encrypt a message and sends this message to Lionel
- Lionel decrypts the message sent by Tom thanks to his private key
Important : if the public key was sent via an unsecured network, Tom must ask Lionel if the public key he received is the correct one.
This ensures that the public key has not been modified by a hacker who has succeeded in intercepting it.
Following example : Lionel wishes to reply to Tom :
- to start, Tom needs to generate a key pair (public key / private key)
- Lionel asks Tom for his public key and encrypts his message using this public key
- Tom decrypts Lionel's message using his private key
Microsoft recommends using RSA because DSA is less secure than RSA.
Also, Diffie-Hellman can only be used to generate keys.
4. Digital signatures
With asymmetric encryption (or public key encryption), you can also create digital signatures.
These digital signatures (or certificates) will allow you to verify the identity of a sender (if their public key is reliable), as well as the integrity of the data.
Thanks to the sender's public key, the recipient can verify that the data received has indeed been sent by the right person (and not by a hacker trying to impersonate them).
To digitally sign a message, the sender must create a digest of their message.
For this, he will use a hashing algorithm and apply it to his message.
Then, the sender must encrypt this synthesis using his private key to create his own signature.
When the recipient receives the message and the signature linked to it, he must decrypt the signature using the sender's public key to recover the summary of the message received.
Then, the recipient hashes the digest of the received message using the same algorithm used by the sender.
If the summary of the message calculated by the recipient matches that conveyed by the sender, the recipient knows that the message was sent by the right person.
Note that a digital signature can be verified by anyone since the public key is obviously public.
This digital signature process therefore only verifies the identity of the sender of the data.
If you want the data sent not to be readable by anyone, you must also encrypt the data to be sent.
5. Hash values
As explained earlier, to create a digital signature, the sender must use a hash algorithm.
Hash algorithms make it possible to obtain a binary value of fixed length from any binary value (text, file, ...).
When you hash a variable length value, you will always get a hash value with a fixed length.
This hash value is unique and will change if any bit or letter is changed in the source text.
With a hardened hash function, the hash value can change by up to 50% if even the smallest bit is changed in the hashed binary value.
Technically, hashing 2 different binary values will always result in 2 different hash values.
Although the risk of collision (2 binary values producing the same hash value) exists for older hashing algorithms, such as MD5. But this is very rare.
Note that for the sending of the message to be completely secure (confidentiality, integrity, authentication, ...), you must use a digital signature (a certificate) and encryption.
Important : MD5 and SHA-1 hashing algorithms have been detected as insecure. SHA-2 (which corresponds to SHA256, SHA384 and SHA512) is therefore recommended.
Moreover, Microsoft Edge blocks websites whose SSL certificate used with the HTTPS protocol uses a hash algorithm.
6. Generating random numbers for encryption
For data encryption to be as efficient as possible, it's important that the key or keys used for encryption are generated as randomly as possible.
Avoid using handwritten values such as "1234" or "mytoppassword" as an encryption key and instead use random values obtained from a random number generator.
Thus, it will be almost impossible to predict what was the output value of the random number generator used.
Source : Overview of encryption, digital signatures, and hash algorithms in .NET - Microsoft Docs.
Share this tutorial
To see also
-
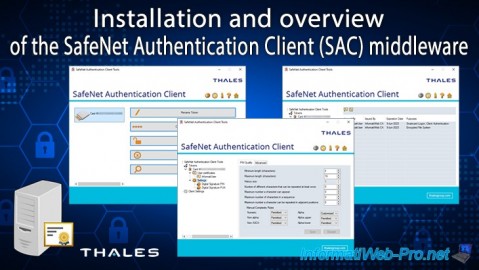
Articles 1/26/2024
SafeNet Authentication Client (SAC) - Installation and overview
-
Windows Server 12/29/2023
WS 2016 - AD CS - Backup and restore a certificate authority (CA)
-

Windows Server 1/19/2024
WS 2016 - AD CS - Buy smart cards and log in via them
-

Windows Server 1/5/2024
WS 2016 - AD CS - Create a recovery agent to recover certificates

You must be logged in to post a comment