- Linux
- 11 January 2014 at 21:31 UTC
-


- Define a static IP address
- Updating the package list
- Install SSH server (openssh-server)
- Configuring the SSH Server (Optional)
- Secure your SSH server
- Connect to the server via SSH
- Enable the firewall
1. Define a static IP address
Since our Ubuntu machine will act as server, it's strongly recommended him to set a static IP address.
To do this, read our tutorial "Ubuntu - Define a private static IP address".
2. Updating the package list
For safety, we put first update the package list and then to retrieve the latest version of the SSH server.
Bash
sudo apt-get update
3. Install SSH server (openssh-server)
Instal the SSH server.
Bash
sudo apt-get install openssh-server
4. Configuring the SSH Server (Optional)
Now that the SSH server is installed, you can remotely connect to your Ubuntu machine via accounts enabled on this machine.
By default, the root account is disabled in Ubuntu but it can be used for SSH connection if it is enabled.
To enable the root account, follow our tip "Ubuntu - Enable the root account".
To configure the SSH server, you must edit the configuration file "sshd_config" found in the file "/etc/ssh/".
Bash
vi /etc/ssh/sshd_config
Locate the "Authentication" and change if necessary the 2 following informations :
Bash
# The time a user has to log on after this time the server will cut the connection. # If you want to disable this period and allow the user to take his time, he must set this parameter to 0 # The default is 120 seconds (2 minutes) LoginGraceTime 120 # Allow or disallow the use of the root account for SSH connection # Prevent use the root account for the connection may be a safety measure to prevent a hacker connects remotely with this account and have all the rights on the Ubuntu server. PermitRootLogin yes # To enable connection to the server using the root account without a password, you must set the parameter above to "without-password". # WARNING: The root account has full rights on your server and the user logs in with that account can therefore do whatever he wants. # This parameter is used only during testing but it should never be used in production. PermitRootLogin without-password
5. Secure your SSH server
To secure SSH, we recommend that you change the server port and prohibit the use of the root account (which has the power of life and death on your server) to connect to the server through SSH.
To do this, create a new user :
Bash
adduser informatiweb
Then, enable root account on the server to use it using the command "su -".
Then, edit the configuration file "/etc/ssh/sshd_config" of the SSH server, like this :
Bash
# Change the port of the server (as everyone knows) Port 2222 # Disable the connection with the root user PermitRootLogin no # And add a list of authorized users (separated by a space) AllowUsers informatiweb
Finally, restart the ssh server to reflect the changes.
Bash
sudo service ssh restart
6. Connect to the server via SSH
To connect to the SSH server, nothing more simple. Simply download an SSH client for your operating system and connect to your server by its IP address (or domain name if applicable). Then log in with the accounts of the Ubuntu server or the root account if you have allowed in the configuration of the SSH server (by default its use is permitted by the SSH server, but the account is disabled in Ubuntu).
On Windows, use the customer "PuTTY" (direct link).
On Mac and Linux, use the "ssh" command like this :
Bash
# Login ssh informatiweb@192.168.1.20 # Logout exit
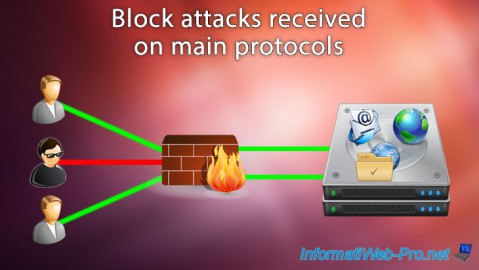
7. Enable the firewall
If you want to enable the firewall Ubuntu, make sure to allow the SSH server in the firewall before activating.
Otherwise, your SSH connection will be terminated and you will not know to access your server remotely.
To know the name of an application, just type the following command :
Bash
sudo ufw app list
Now you know that the SSH server is called "OpenSSH". To allow this, type this :
Bash
sudo ufw allow "OpenSSH"
To be sure that "OpenSSH" is authorized, simply retype the command above. Ubuntu you should now see this :
Bash
Missed adding the existing rule Missed adding the existing rule (v6)
You can now activate the firewall using the command :
Bash
sudo ufw enable
If you use this command remotely via your SSH connection, you will need to meet more "y" to the following question :
Bash
The command can interrupt existing ssh connections. Perform the operation (y|n) ?
Share this tutorial
To see also
-

Linux 2/25/2015
Debian - Install and secure a complete mail server
-
Linux 7/7/2015
Debian / Ubuntu - Block attacks (mail, web and FTP)
-

Linux 10/11/2016
Debian / Ubuntu - Configure an iSCSI server and an iSCSI client
-
Linux 10/2/2016
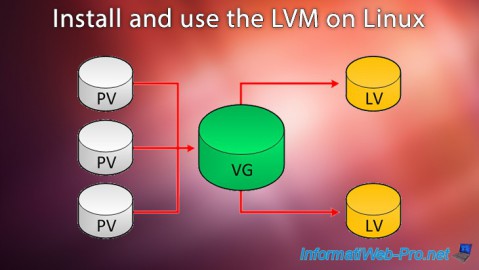
Install and use the LVM on Linux


You must be logged in to post a comment