Install, configure and deliver applications with Citrix XenApp 7.6
- Citrix
- Citrix XenApp / XenDesktop
- 22 March 2015 at 12:23 UTC
-

- 3/4
7. Securing StoreFront (HTTPS)
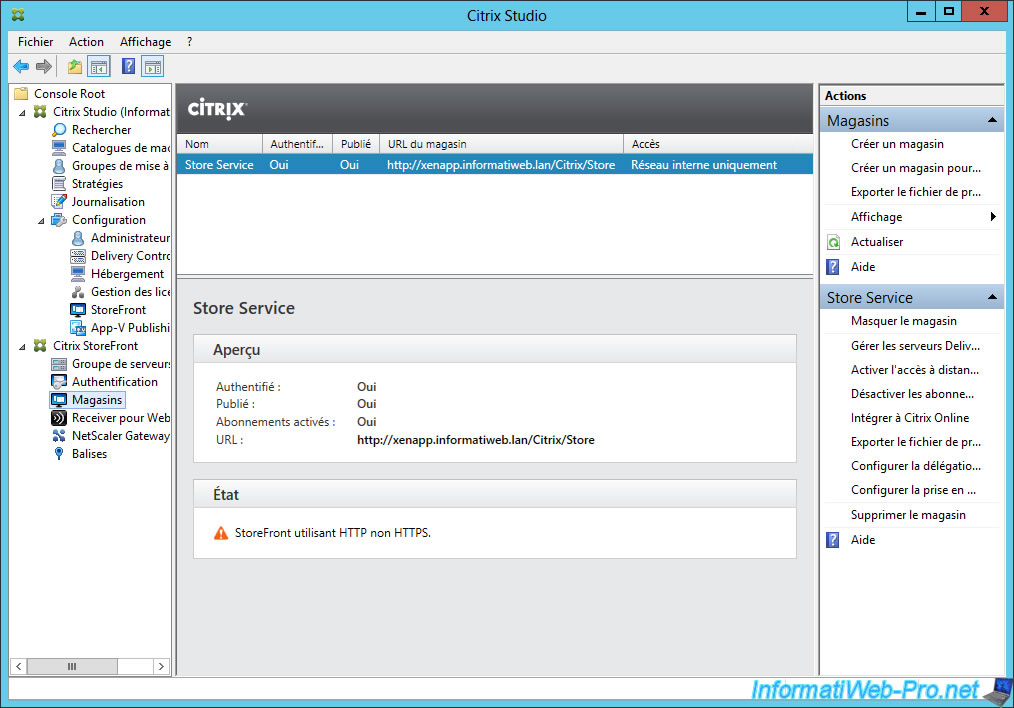
For now, StoreFront works with HTTP (unsecured) instead of HTTPS (secure).
To secure StoreFront, simply secure the IIS web server with a valid certificate.
Which involves 4 conditions :
- the certificate must not be self-signed
- the certificate must be signed by a certification authority recognized by the client computer
- the certificate revocation lists must be available.
- the certificate must not be revoked
If you want to create a root CA on your local network, follow this : Windows Server 2012 / 2012 R2 - Create an Enterprise Root Certification Authority (Root CA)
If you use your own root CA to sign your certificate, you must import the certificate of your authority in the Trusted Root Certification Authorities of client computers.
For this, you have 2 options :
- do it manually : Import a certificate (of a root certification authority) in the trusted certificates list of Windows
- join the client computer, to the Active Directory to do this automatically through GPO : Distribute the certificate to the Active Directory clients
If you use a certificate signed by Symantec SSL, GeoTrust or another certification authority recognized by everyone, you will have no certificate problem.
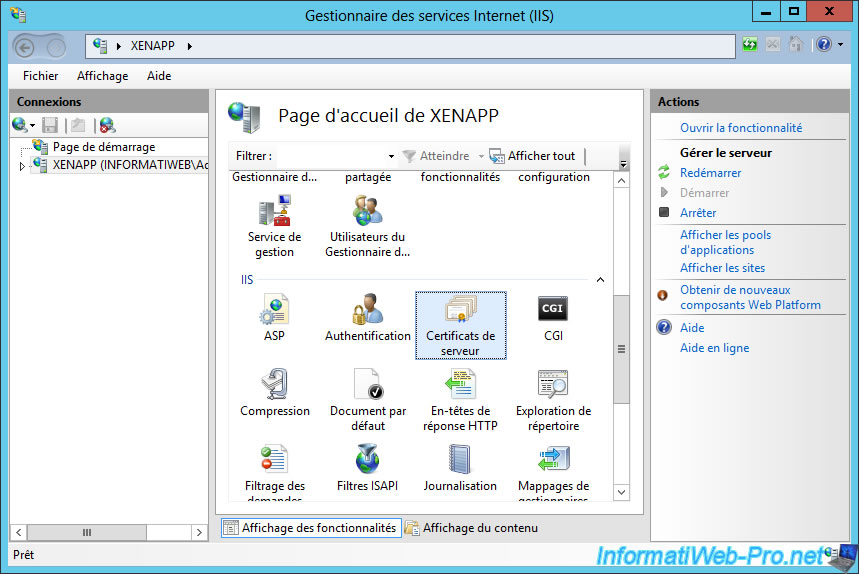
To request a certificate from your CA, first run the "Internet Information Services (IIS)".
Click the name of your server and go to "Server Certificates".
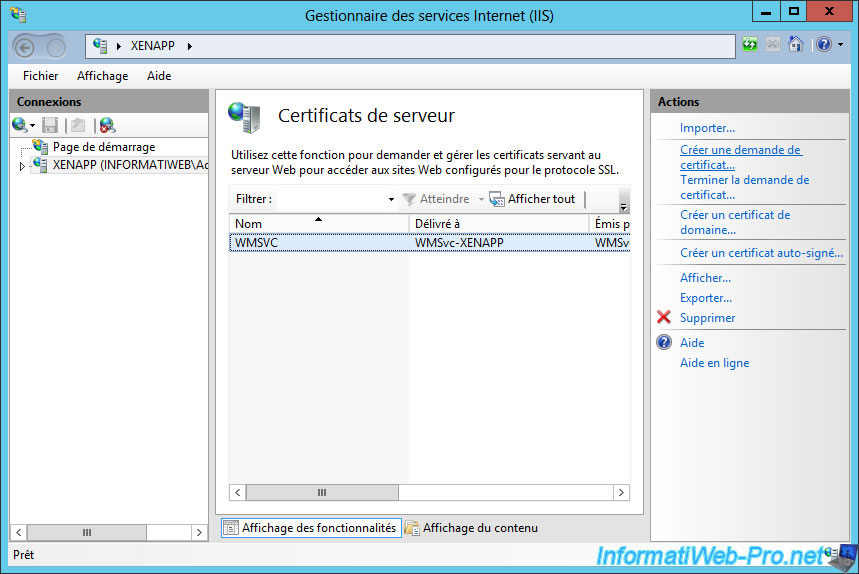
Click "Create a certificate request" in the right column.
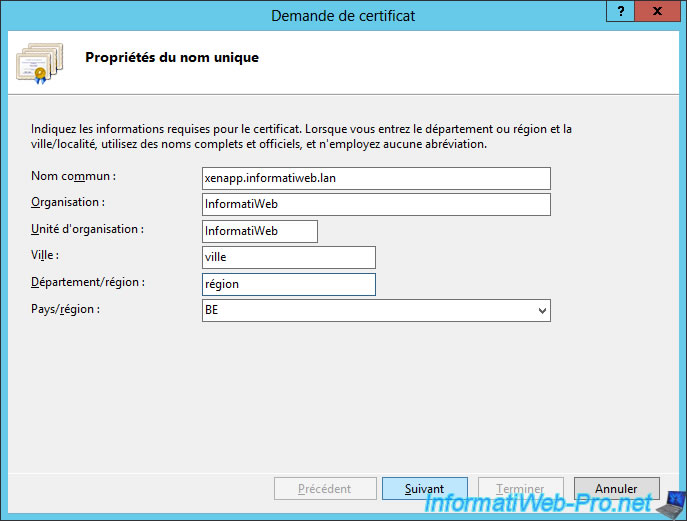
The information verified for this certificate is the common name. In this case, it's the domain name of the server where you installed StoreFront.
For others informations, indicate preferably real information.
If you send this request to an officially recognized certification authority, you must use the real information.
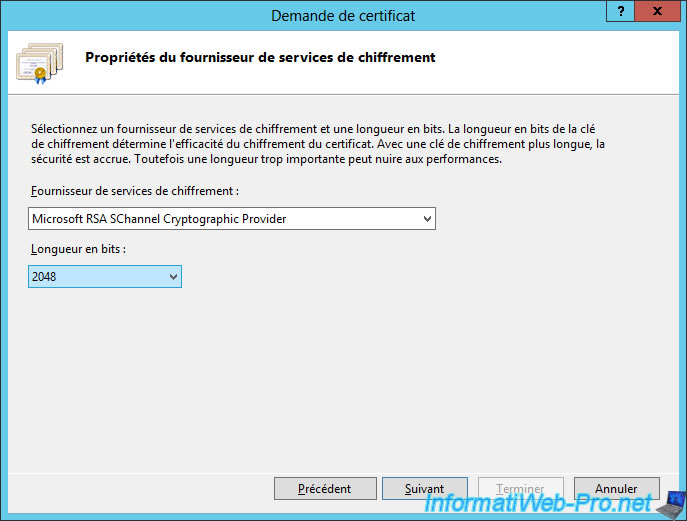
Choose the right size for the encryption key. By default, IIS selects the length of 1024-bit.
Nevertheless, our root certificate authority that we have created, requires a 2048-bit key.
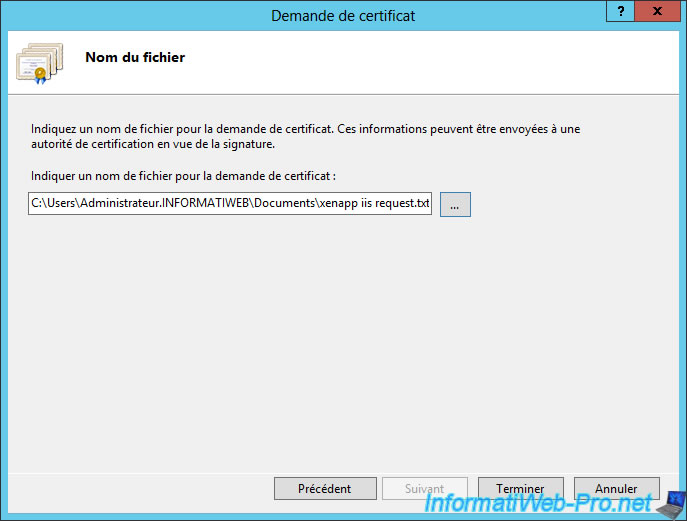
Save this request in a ".txt" file.
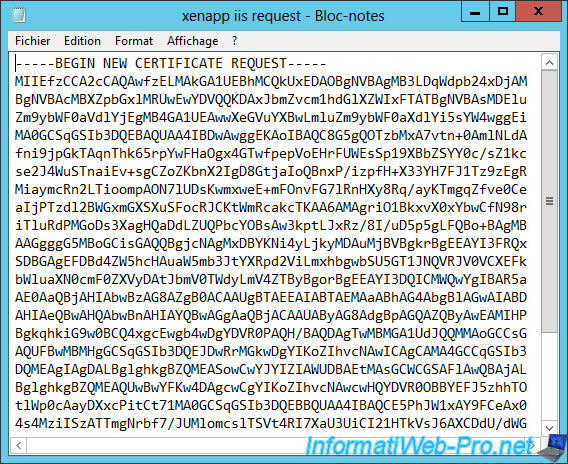
If you open this file, you will see that your certificate request has been encoded in base 64.
Go to the website of the certification authority that you want and paste this request on their website.
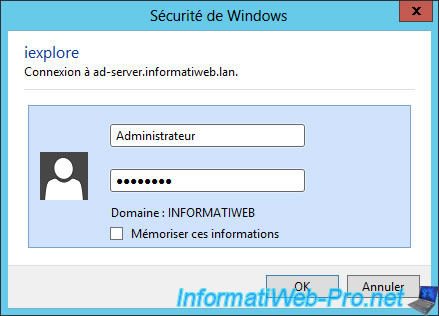
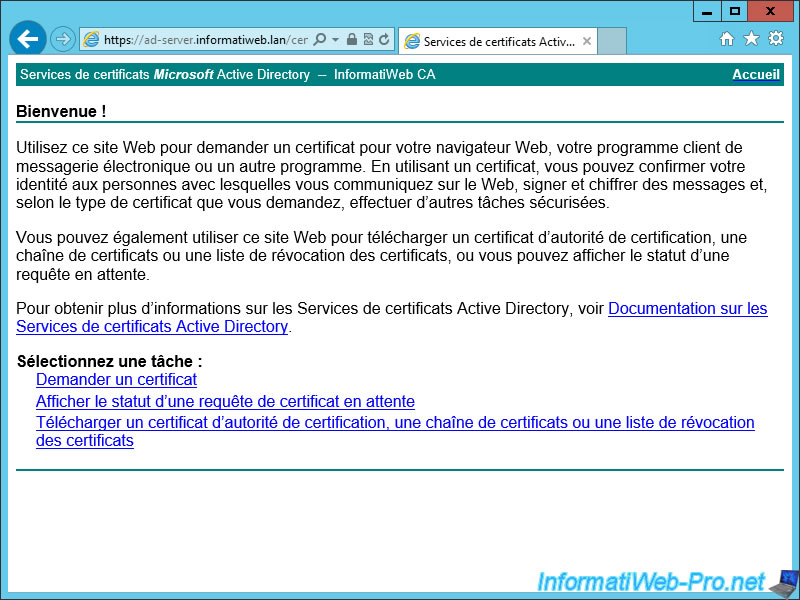
In our case, we will connect to the web interface of our certification authority.
We use the Administrator account of our domain.
On this page, click on "Request a certificate".
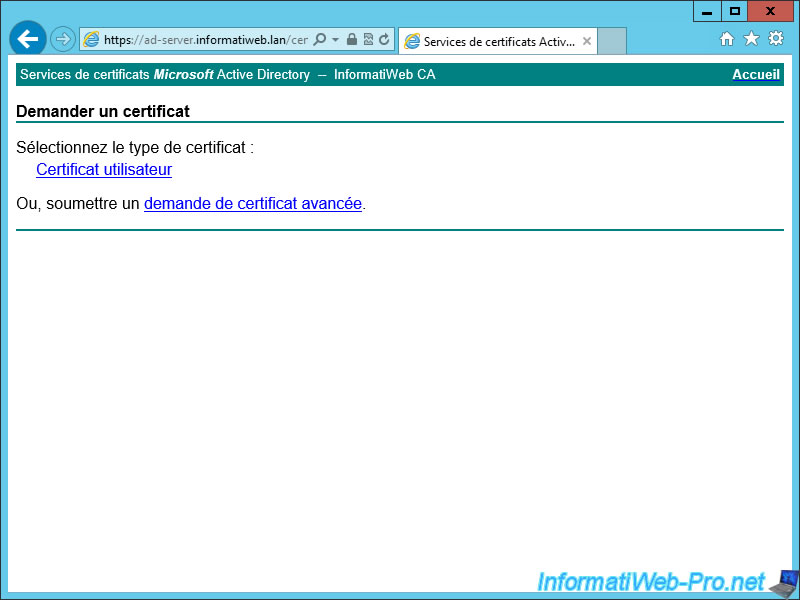
Then : Advanced Certificate Request.
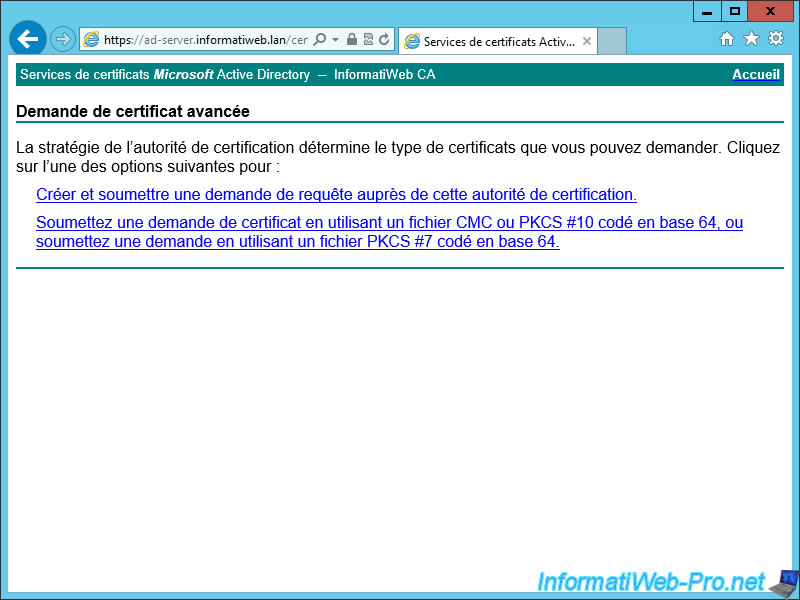
Finally, click on the last link (Submit a request using a PKCS #7 coded in base 64).
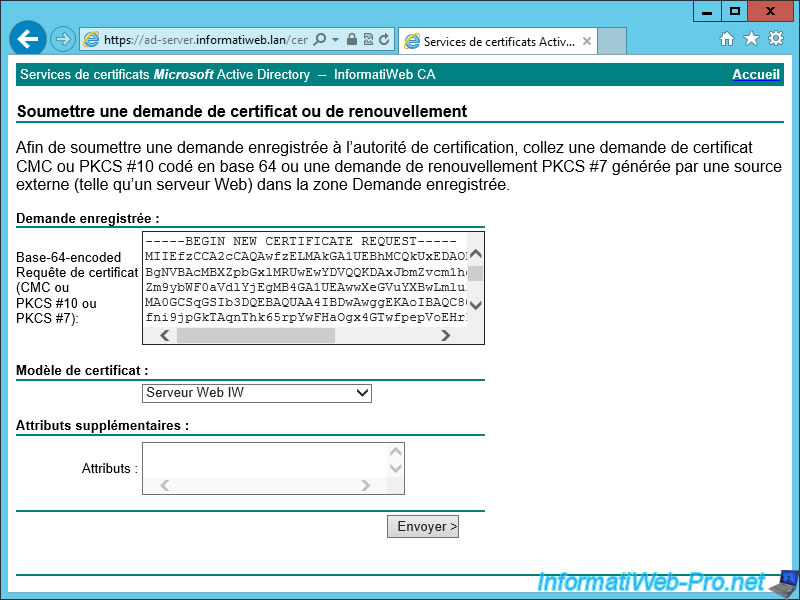
Paste the request in the case and select the template to use. In our case, we had duplicated the model "Web Server" in "Web Server IW".
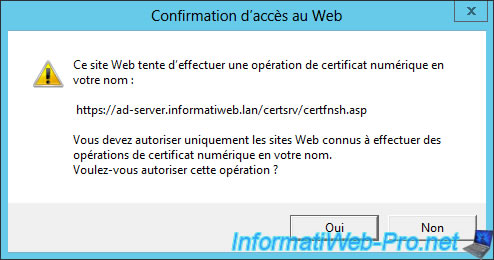
Internet Explorer will warn you that this website attempts to perform a numerical operation on your behalf. Click "Yes".
And finally, download the certificate.
Note : The certificate chain would serve if you created a secondary certification authority.
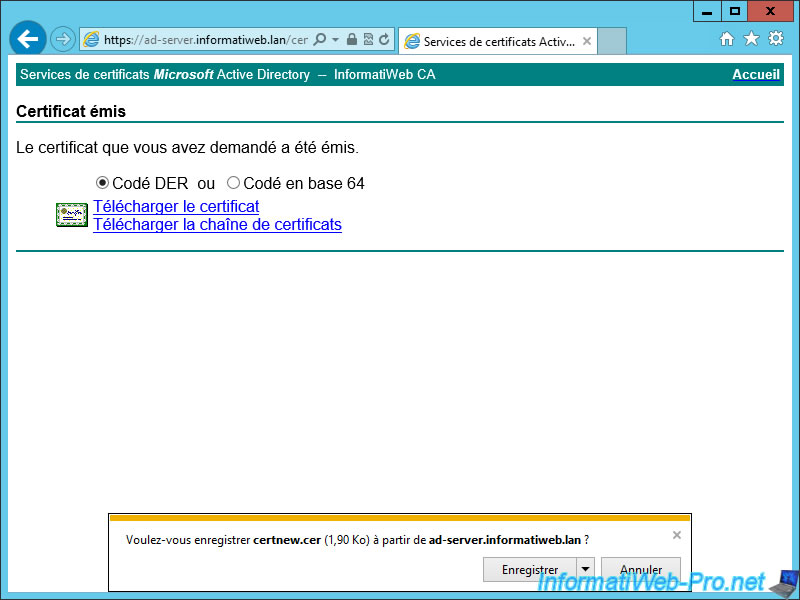
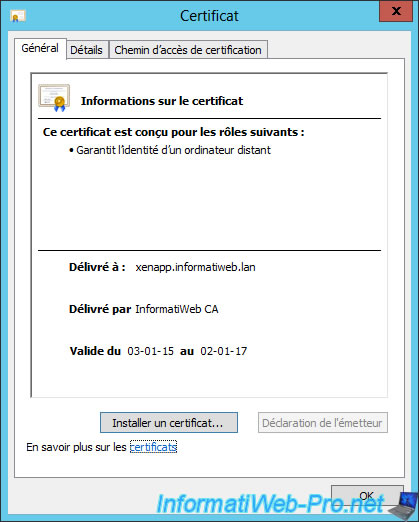
If you open this certificate, you will see that it was issued for "common name indicated in the request" and issued by "Authority who signed your certificate".
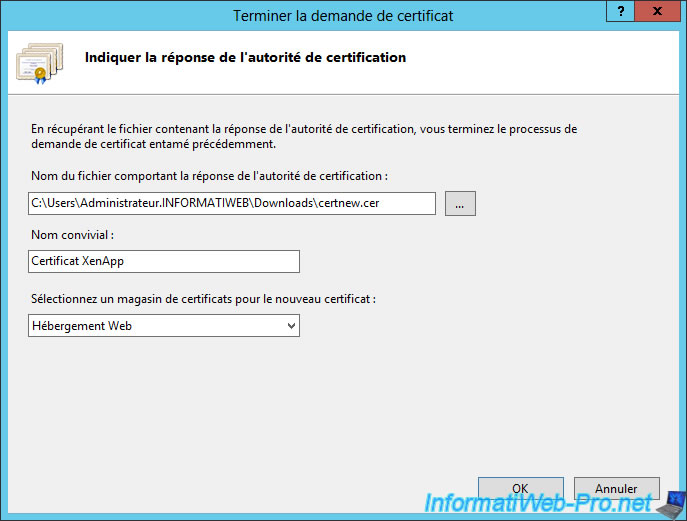
Go back to the Internet Services Manager (IIS) and click "Finish the certificate request".
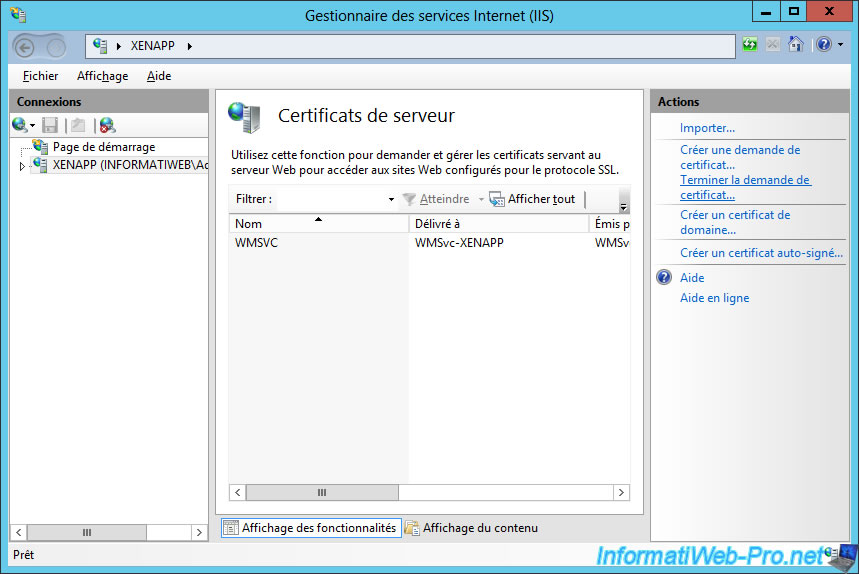
Select the certificate you just created (or receive from a certification authority).
Enter a name (no matter which one) and choose Web Hosting (this choice doesn't affect the functioning of the certificate).
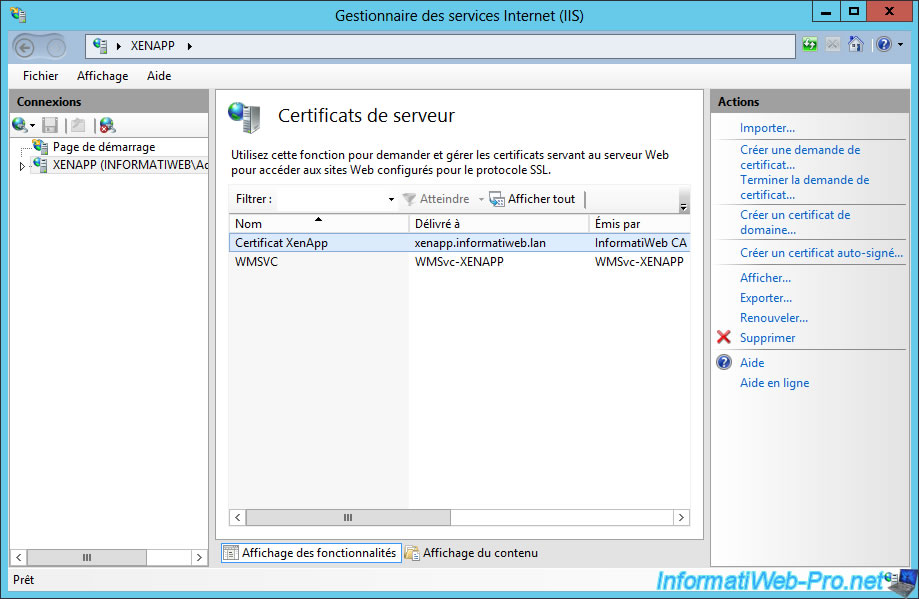
Your certificate appear in the list of server certificates.
Now, select the "Default Web Site" and click on "Connections" in the right column.
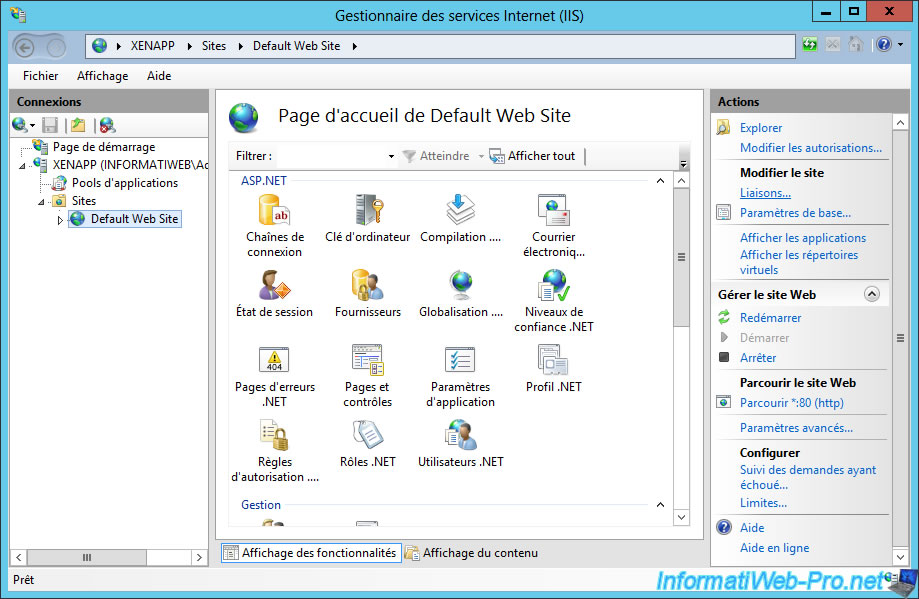
Click on "Add".
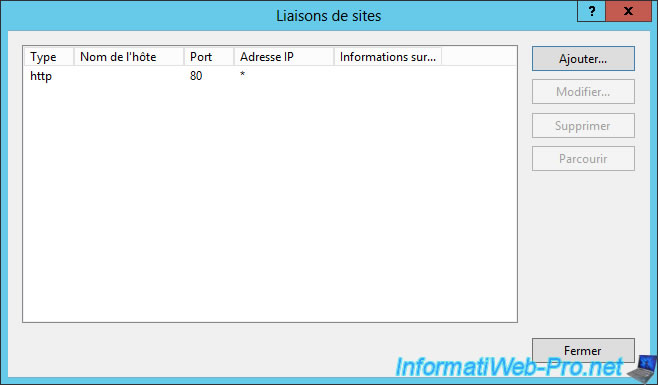
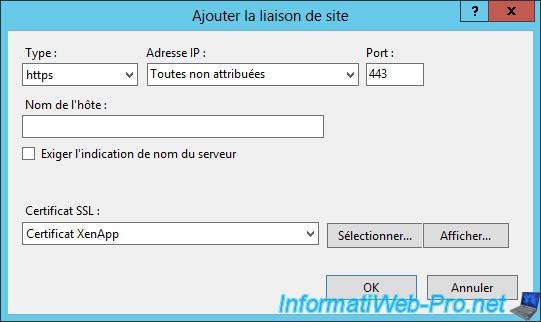
Select "Type : https" and select your SSL certificate in the list.
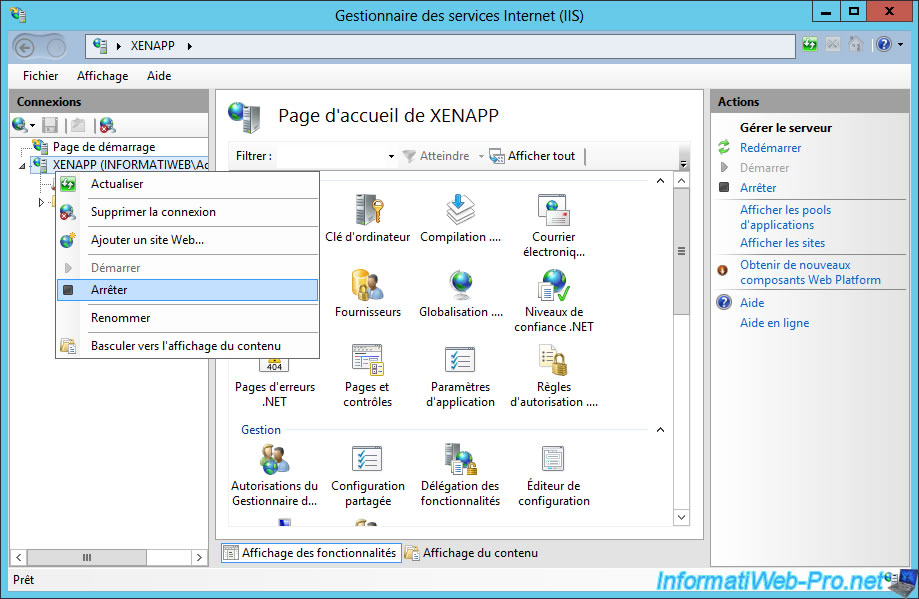
Restart the IIS server.
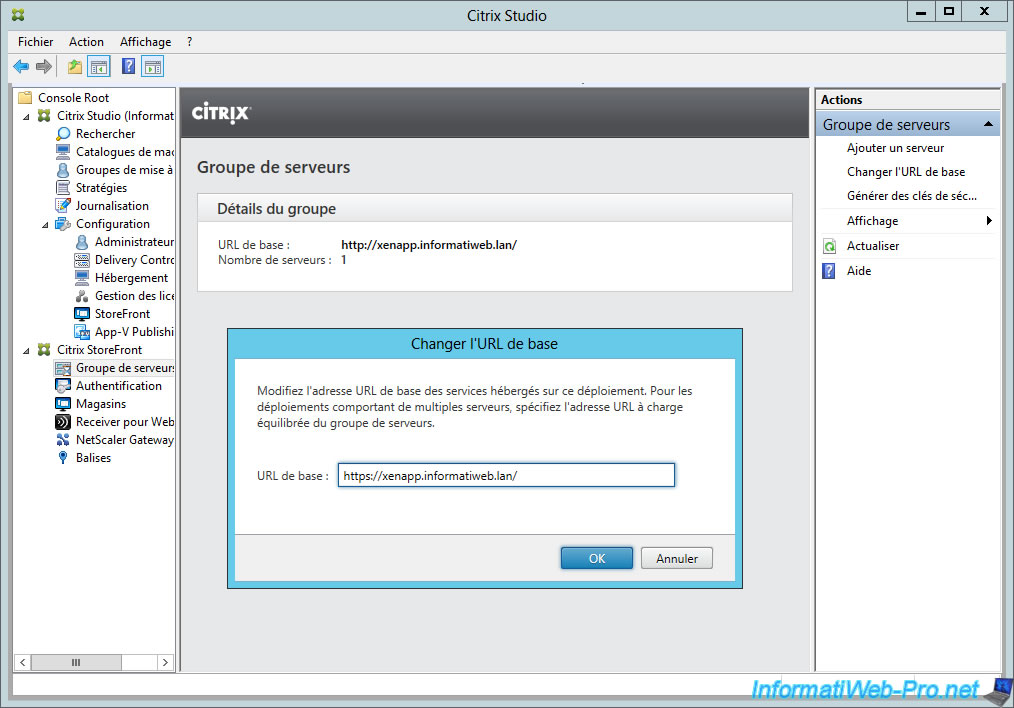
Don't forget to change the base URL of StoreFront by going to "Citrix StoreFront -> Servers group -> Change the base URL".
Add an 's' for that the URL starts with "https://".
Notes :
- If you do not change the "http" protocol to "https", the web interface will show the url "http" in the configuration file. And Citrix Receiver will consider the SSL certificate as invalid (this is normal, since the http protocol doesn't use certificate).
- Citrix Receiver requires the protocol "https" to run.
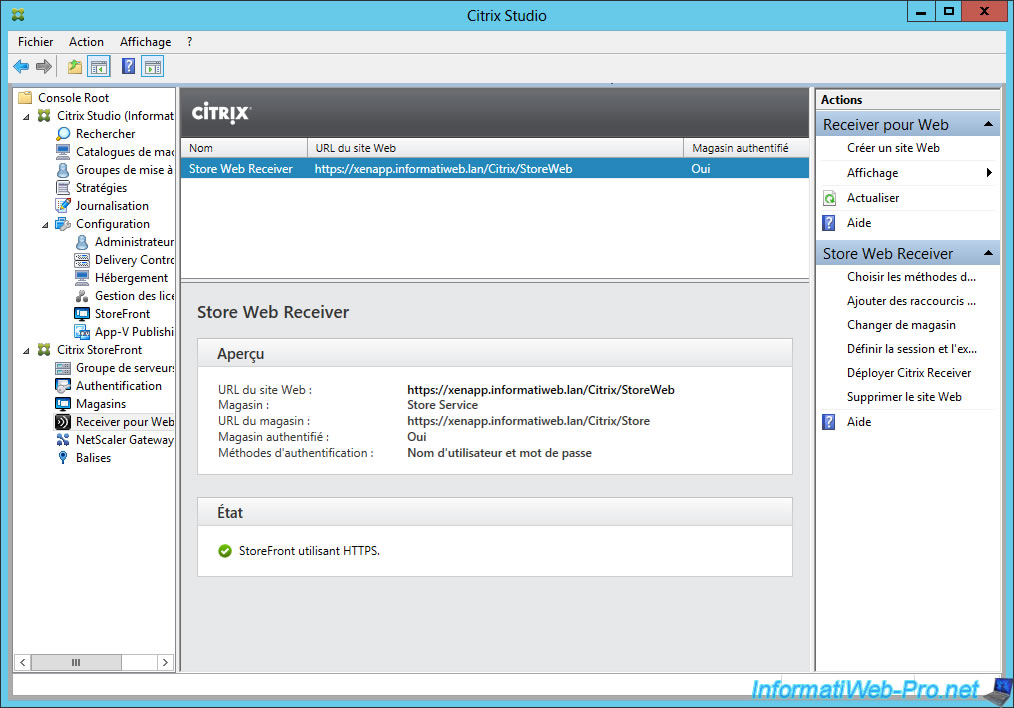
Now, Citrix Studio shows you that StoreFront uses HTTPS.
8. Installation and test of the client : Citrix Receiver
To download and install Citrix Receiver :
- Either you download it from the Citrix website
- Either you download it from the StoreFront server (use the address ending by "StoreWeb" and not "Store").
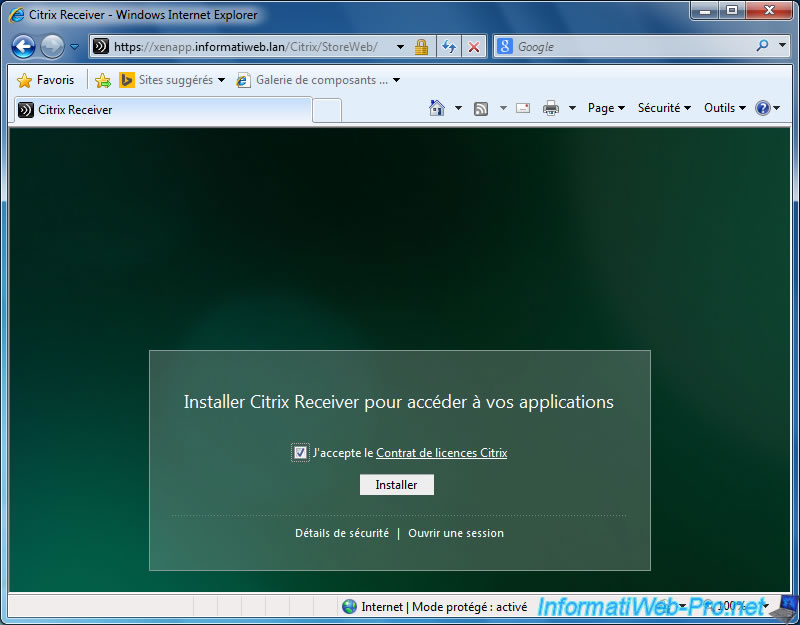
By default : https://xenapp.informatiweb.lan/Citrix/StoreWeb
On the StoreFront page, check the box and click "Install".
Note : if your web browser displays an error about the server's SSL certificate, make sure that :
- the SSL certificate used is issued by a recognized certification authority
- or the certificate of your CA is located in the trusted certification authorities of Windows, if you are using an SSL certificate from your CA.
IMPORTANT : if your web browser displays an error about the server's SSL certificate, the access to applications and virtual desktops from Citrix Receiver will not work.
As you can see, the program is downloaded from your server.
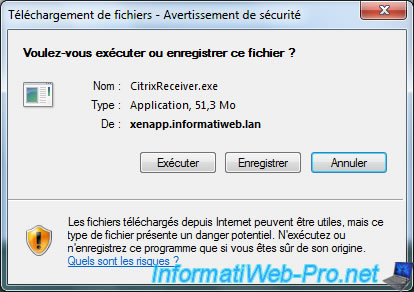
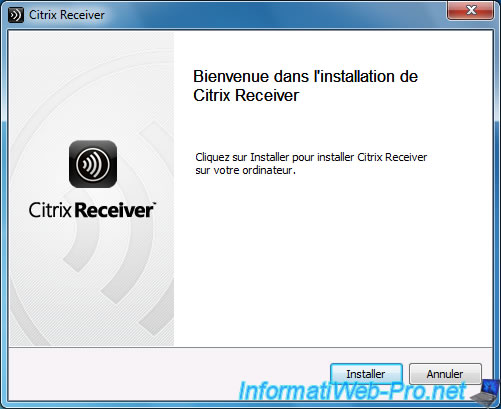
Install Citrix Receiver.
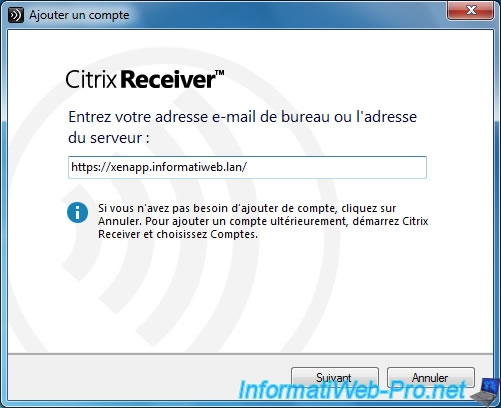
Click "Add Account".
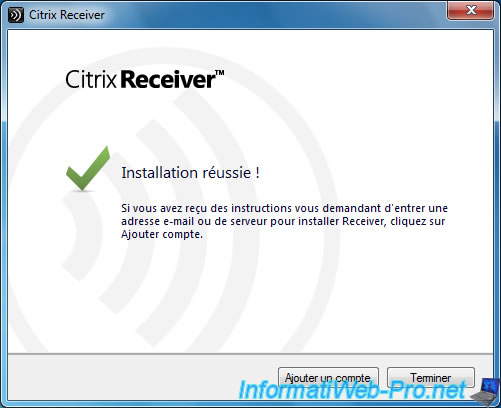
Then, enter "https" address of your StoreFront server.
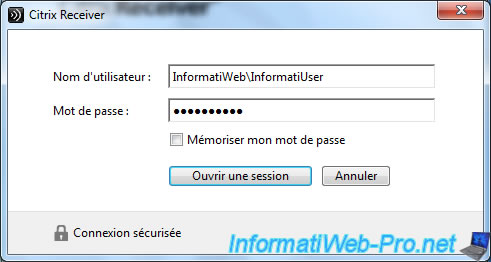
Connect with the Active Directory user.
Preferably, a user authorized to use the applications and / or desktops published.
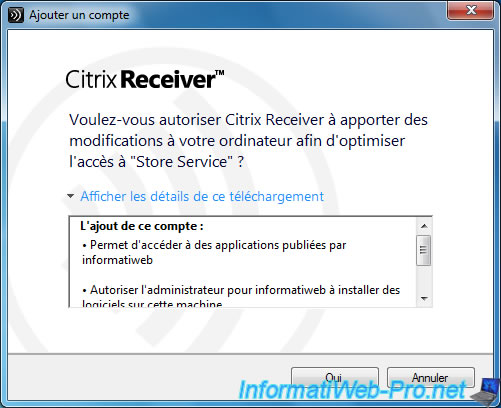
Click "Yes".
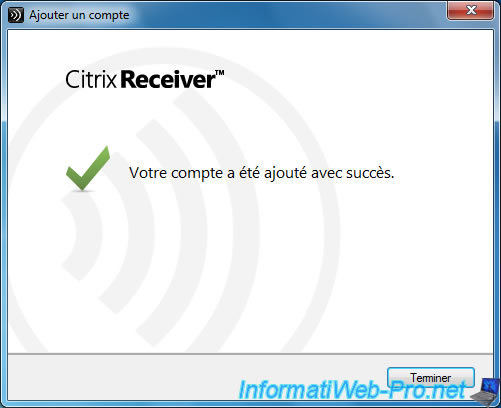
Citrix Receiver is configured.
To access published applications (those that you can use), click the + icon.
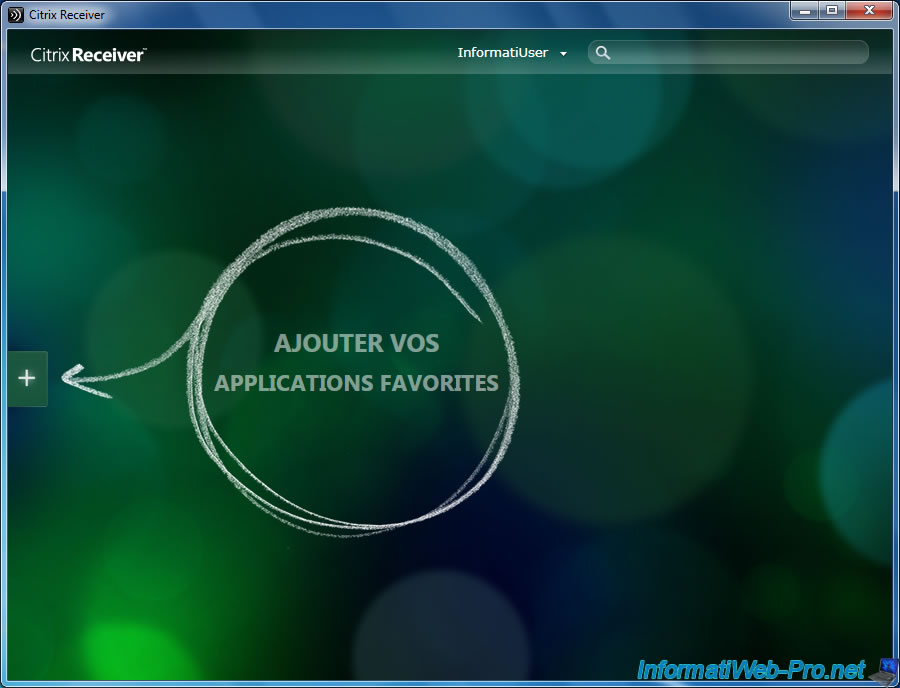
Click applications and / or desktops to add shortcuts in Citrix Receiver.
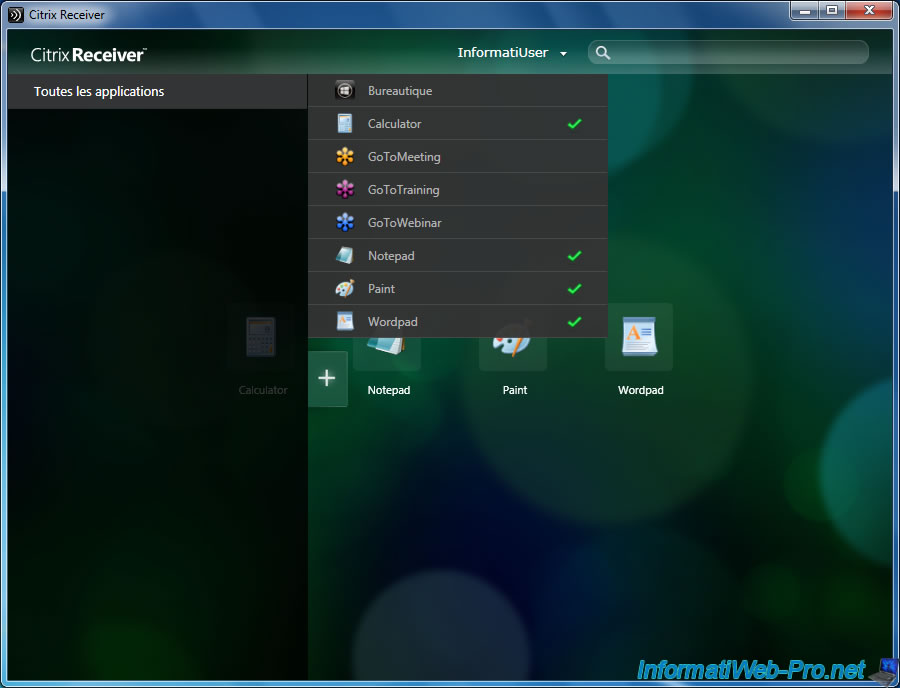
And try to launch applications.
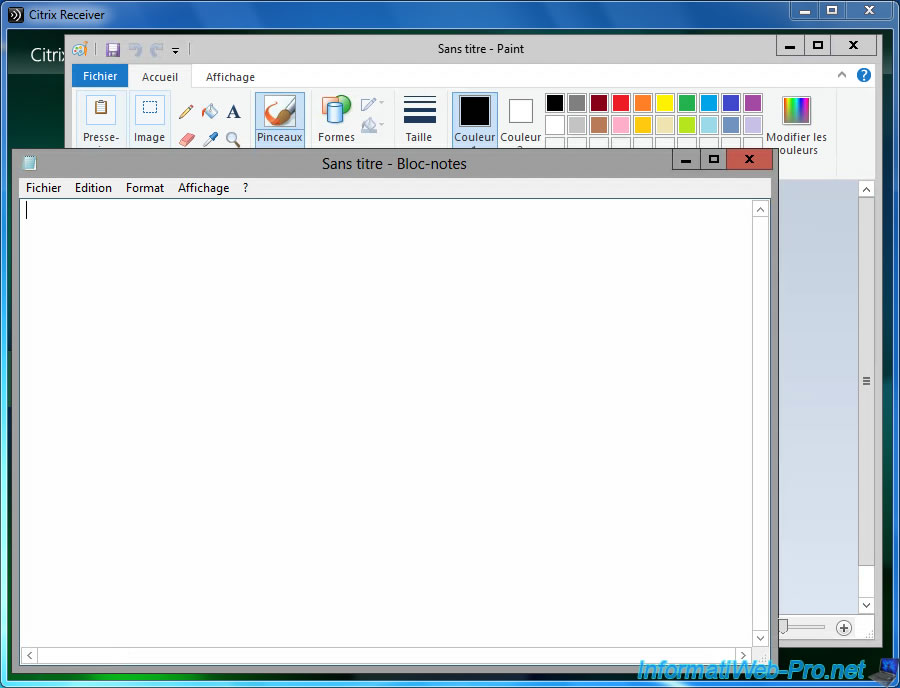
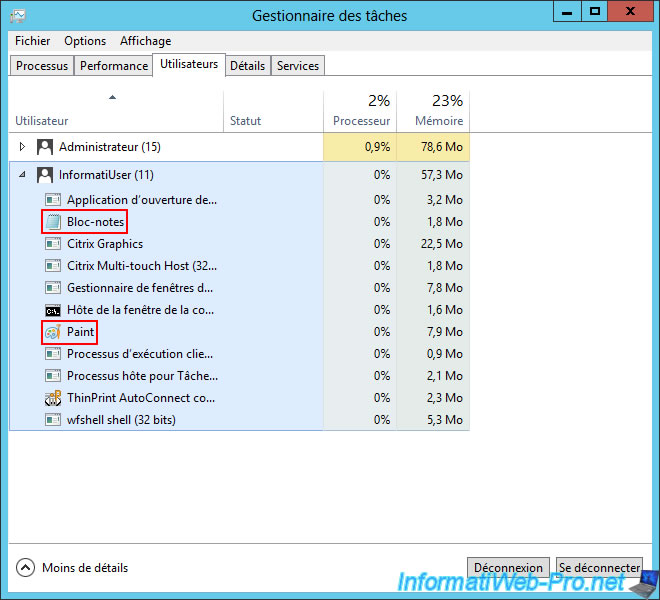
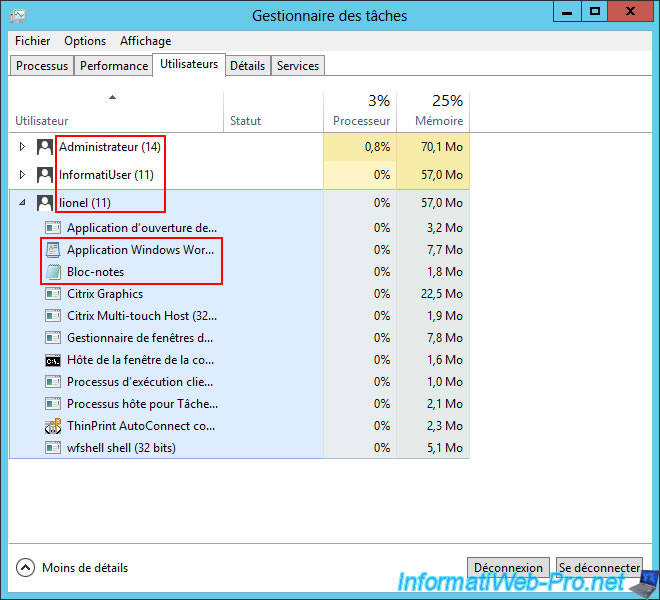
If you go to the task manager of the server where you installed the Virtual Delivery Agent, you will see that a session (with your Active Directory user name) is open and it uses applications that you have launched.
This proves that these applications run on the server and not on the client.
9. Multi-session test on a Windows Server Machine
If you installed the Virtual Delivery Agent on a machine running Windows Server, you can open multiple sessions simultaneously.
For this, we launched the "Notepad" and "Paint" with the user "InformatiUser".
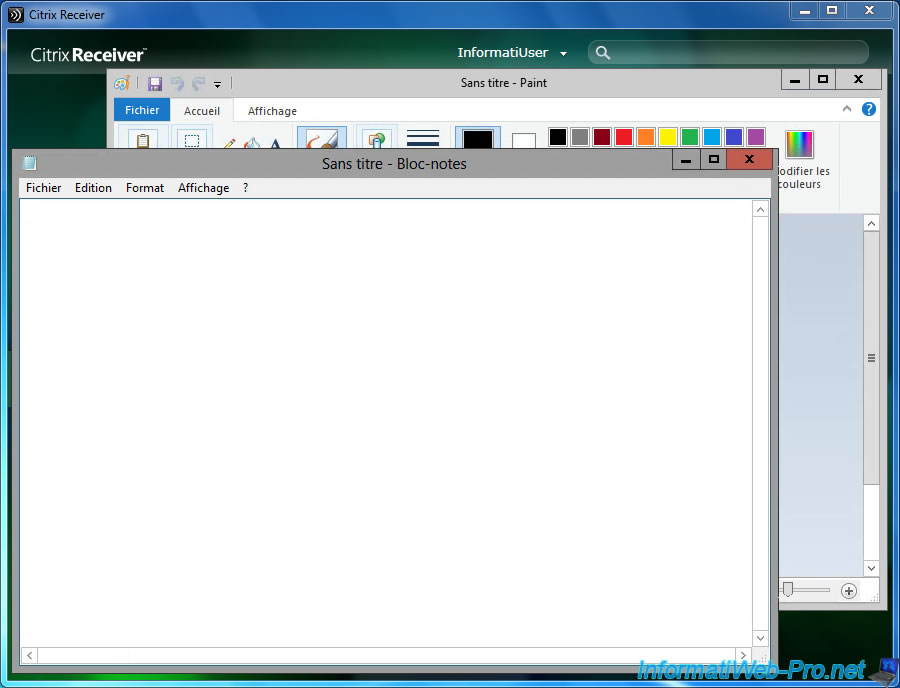
And applications "WordPad" and "Notepad" with the "Lionel" account.
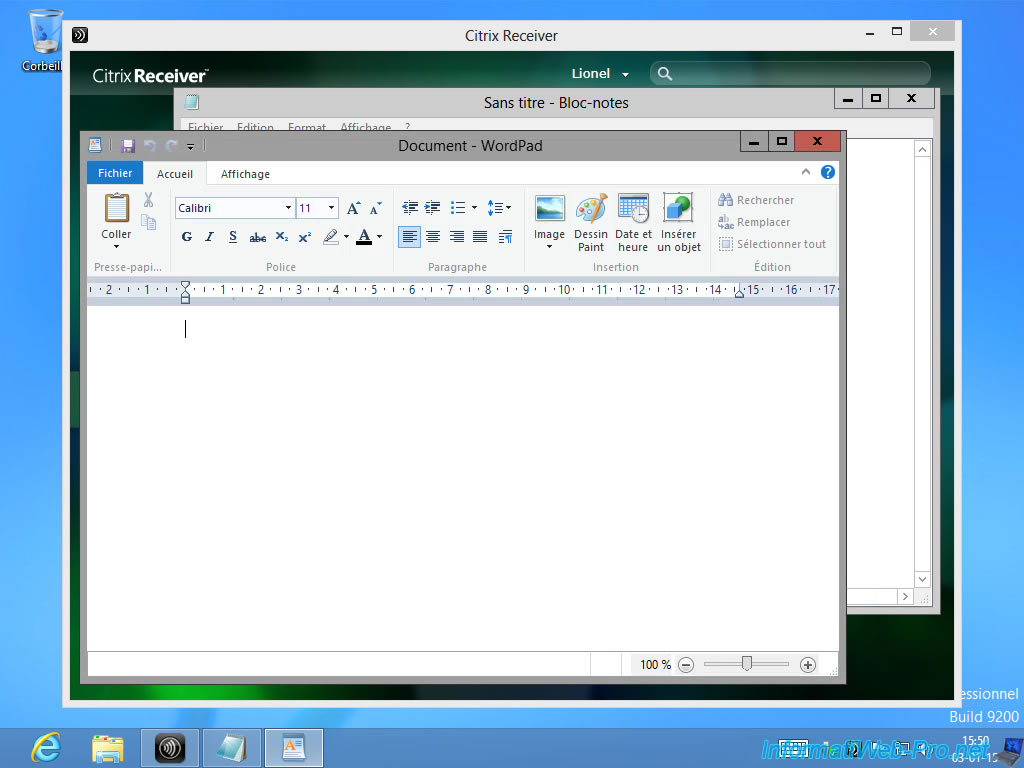
On the server, we see that these two sessions are open on the same server and each application uses this server.
Note : The user "Administrator" is connected locally to show you this information. That said, no need to connect locally for the server is working correctly.
Share this tutorial
To see also
-

Citrix 4/9/2016
Citrix NetScaler Gateway 11.0 - Configuration and integration with XenApp/XenDesktop
-
Citrix 5/14/2016
Citrix XenApp / XenDesktop 7.6 - Load balancing
-
Citrix 5/31/2015
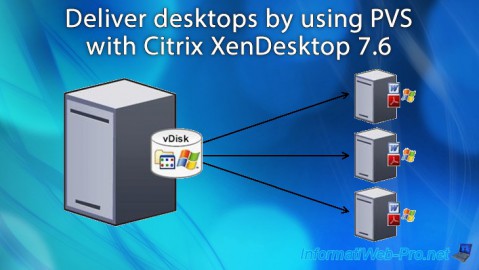
Citrix XenDesktop 7.6 - Deliver desktops by using PVS
-

Citrix 3/27/2016
Citrix XenDesktop 7.6 - PVS - vDisks updates

No comment